Network Home

What steps can I take to secure my home network ?
Securing your home network is crucial in today's digital age where cyber threats are constantly evolving. Here are some steps you can take to ensure the safety and privacy of your home network: Change default router settings, use strong encryption, set up a guest network, update device software, use firewall and encrypt data, secure your wireless signal, control device access, and monitor network activity. By following these steps, you can significantly enhance the security of your home network and protect your personal information from potential cyber threats.
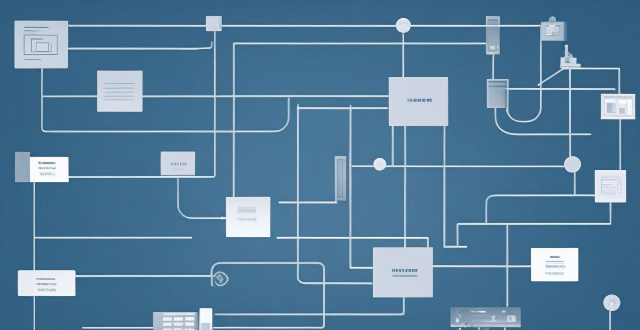
Can you explain the function of a network switch in a home network setup ?
The article discusses the function of a network switch in a home network setup. The primary function of a network switch is to connect multiple devices together, either through Ethernet cables or wireless connections. It also manages data traffic within the network by forwarding data packets to their intended destination based on their IP address. Additionally, network switches enhance network performance by providing dedicated bandwidth to each connected device and prioritizing certain types of traffic over others. Finally, network switches come with various security features that help protect your home network from unauthorized access and cyber threats.
How can I reduce network latency in my home ?
To reduce network latency in your home, check your internet speed, upgrade your router, use wired connections, optimize router settings, limit bandwidth hogs, place your router strategically, use a Wi-Fi extender or mesh network, and close unused applications and tabs.
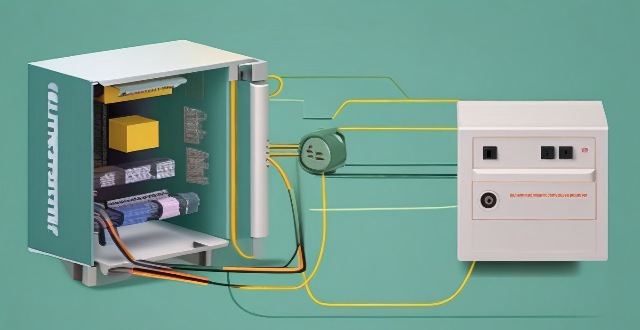
What are the benefits of using a powerline adapter for home network connectivity ?
Powerline adapters offer a simple and effective way to enhance home network connectivity by using existing electrical wiring. They provide benefits such as ease of installation, stable connections, extended coverage, high performance, and cost-effectiveness.
How can I improve my home network with Wi-Fi 6 ?
Wi-Fi 6, also known as 802.11ax, is the latest wireless networking standard that promises faster speeds, better range, and improved performance in congested areas. If you're looking to improve your home network with Wi-Fi 6, here are some tips: upgrade your router; place it strategically; use Wi-Fi extenders or mesh networks; and optimize your device settings.
How can I protect my home network from cyber attacks ?
The text provides a topic summary on how to protect your home network from cyber attacks. It suggests changing default settings such as passwords and firmware, using strong passwords, securing your Wi-Fi network with WPA2 encryption, keeping devices updated with software patches and antivirus software, and educating yourself and family members about safe online practices. Following these steps can help reduce the risk of cyber attacks and keep personal information secure.

How can I improve my home's Wi-Fi network coverage ?
The text provides tips on how to improve Wi-Fi network coverage at home, including upgrading the router, changing its location, using extenders or mesh networks, updating firmware, adjusting settings, limiting bandwidth-heavy activities, replacing old devices, and using wired connections where possible.

How does a network bridge improve internet connectivity ?
A network bridge is a device that connects two or more networks at the data link layer, offering benefits such as reduced congestion, increased security, enhanced performance, cost-effectiveness, and compatibility. It improves internet connectivity by segregating traffic, filtering based on MAC addresses, optimizing routing, and extending the use of existing infrastructure. Bridges are applicable in home, enterprise, and public access networks for connecting devices, separating departmental networks, and providing guest access.
What strategies can be implemented to optimize wireless network connectivity ?
Optimizing wireless network connectivity is crucial for seamless internet access. Strategies include choosing the right location for the router, updating firmware and drivers, changing the wireless channel, using quality hardware, implementing Quality of Service (QoS) settings, securing the network, and reducing interference from other devices and appliances. These steps can improve wireless network performance and ensure efficient internet access.
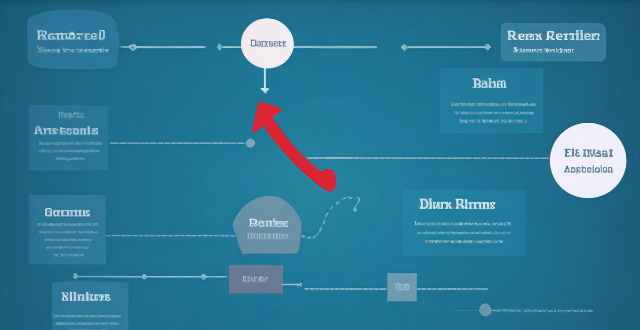
What is the difference between a router and a modem in network connectivity ?
The text delineates the differences between a router and a modem, highlighting their distinct roles within a network. A modem primarily converts digital signals to analog for transmission over telephone lines or cables, while a router creates a local area network (LAN) that enables multiple devices to connect and communicate with each other and the internet. Combination devices that integrate both functionalities are also discussed, noting their convenience but potential lack of advanced features compared to separate units. Understanding these differences is crucial for setting up and maintaining a reliable internet connection.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.
How much does it cost to upgrade to 5G network ?
The cost of upgrading to a 5G network varies depending on several factors, including your current plan, the carrier you are using, and the device you have. If you want to take advantage of 5G speeds, you will need a 5G-compatible device which can range from $200 to over $1000. The cost of upgrading to a 5G plan also depends on your carrier, with some offering unlimited data plans starting at around $70 per month. In addition to a new device and plan, you may also need to purchase accessories such as cases or screen protectors that are compatible with your new device. Finally, if you are installing a 5G network in your home or office, there may be additional costs associated with installation fees or equipment rental fees.

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.

How do I set up parental controls on my home network connection device ?
Setting up parental controls on your home network connection device is crucial for ensuring a safe online experience for your children. Here's a summary of the steps you should follow: 1. Access the router settings by typing in its IP address and entering the required login details. 2. Navigate to the parental controls section within the settings menu. 3. Create user profiles for each household member, including name, age, and unique login credentials. 4. Implement time restrictions to limit internet access during certain hours or to set daily/weekly usage limits. 5. Establish content filters to block specific types of websites or content, such as adult material, violence, or gambling. 6. Save and apply the changes, then test the controls to ensure they are functioning correctly. Additionally, it's important to regularly review and update the controls as needed, educate your children about online safety, and consider using additional tools like parental control software for enhanced protection.

Is there a way to check the strength of my internet connection's network coverage ?
Checking the strength of your network coverage is crucial for ensuring reliable and high-quality internet access. Here's a summary of key points from the text: 1. **Importance of Checking Network Coverage**: Strong network coverage ensures better performance, reliability, and accessibility of internet services. 2. **Methods to Check Network Coverage**: - Use network signal strength apps. - Run online speed tests. - Check router indicator lights. - Observe device built-in indicators. - Physically move around to gauge signal strength. 3. **Tips to Improve Network Coverage**: - Upgrade your router. - Optimize router placement. - Use Wi-Fi extenders. - Switch between different bands (2.4GHz and 5GHz). - Reduce interference from other electronic devices. By employing these methods and tips, you can assess and potentially enhance your internet connection's network coverage.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

How can I monitor my home security system remotely ?
This guide provides a comprehensive overview of how to monitor your home security system remotely. It covers choosing a reliable security system, connecting it to the internet, monitoring your home remotely, and maintaining your security system. The guide emphasizes the importance of researching and selecting a suitable security system, establishing a secure internet connection, setting up remote access, viewing live streaming footage, receiving alerts and notifications, controlling your security system remotely, regular maintenance, and software updates. By following these steps, you can ensure the safety and security of your home while away.

What are the benefits of using a 5G network ?
The advent of the 5G network has brought about significant changes in the way we use technology. It offers several benefits that were not possible with earlier networks. Here are some of the key advantages: 1. **Faster Speeds**: Compared to 4G, 5G can provide download and upload speeds that are up to 10 times faster. 2. **Lower Latency**: With 5G, the delay is reduced significantly, making real-time communication more efficient. 3. **Increased Capacity**: 5G networks can handle more devices and connections at the same time. 4. **Improved Reliability**: They use advanced signal processing techniques to ensure stable connections. 5. **New Use Cases**: 5G opens up opportunities for new applications like virtual reality and smart cities.

What are the privacy concerns associated with using smart home devices ?
Smart home devices, while convenient, raise privacy concernsSmart home devices, while convenient, raise privacy concerns security vulnerabilities, raise privacy concerns due to data collection, security vulnerabilities, third-party access issues, lack of transparency from manufacturers, permanent data retention, and evolving legal frameworks. Users should research devices thoroughly and take steps to protect their privacy.
What technology is used to extend network coverage in remote locations ?
In remote locations, several technologies are used to extend network coverage, including satellite internet, wireless broadband (Wi-Fi), cellular data, long-range radio networks (LoRaWAN), and fiber optic cables. The choice of technology depends on factors such as cost, availability, and the specific needs of the users in those areas.

How much does it typically cost to outfit a home with smart gadgets ?
This topic summary provides a comprehensive overview of the costs associated with outfitting a home with smart gadgets. It discusses key factors impacting cost, such as home size, scope of automation, brand choices, and installation fees. The text also breaks down typical smart gadgets and their price ranges, including lighting, thermostats, security systems, entertainment devices, and power solutions. Additional considerations like hubs, connectivity, and subscription services are addressed. Finally, it offers estimated total costs for basic, mid-range, and advanced smart home configurations, emphasizing the importance of planning and budgeting to create a smart home that aligns with individual needs and financial constraints.

How can I integrate smart home devices with my home security system ?
The article provides a step-by-step guide for integrating smart home devices with a home security system, including determining compatibility, selecting the right devices, installing and configuring them, connecting to the security system, and testing the integration. The goal is to enhance safety and convenience by allowing remote control and monitoring of access, video surveillance, sensors, and lighting.
Can network slicing improve internet speed and reliability ?
Network slicing is a concept that divides a physical network into multiple virtual networks, each optimized for a specific use case. This approach can improve internet speed and reliability by enabling efficient resource allocation, enhancing performance through customization and optimization, and improving reliability through isolation and scalability. However, effective implementation requires careful planning and coordination among stakeholders involved in the network infrastructure.