Network Support
Can existing devices support 5G network ?
This article discusses whether existing devices can support 5G network and what factors influence this compatibility. The most important factor determining whether a device can support 5G is its hardware, including the modem, antenna, and other components required for 5G connectivity. Another factor that can affect compatibility is the software on your device, such as an outdated operating system or lack of necessary drivers and firmware updates. Finally, even if your device has the necessary hardware and software, you still need to have a carrier that supports 5G in your area. To check if your device is compatible with 5G, you can check your device's specifications, ensure that it is running the latest operating system and has all necessary drivers and firmware updates installed, contact your carrier to see if they offer 5G service in your area and if your plan includes access to this network, and consult with a professional or contact the manufacturer for assistance.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.

How do firewalls contribute to network security ?
Firewalls are crucial for network security, offeringFirewalls are crucial for network security, offering, blocking unwanted connections, preventing preventing network intrusion, enforcing security policies, providing VPN support, integrating with other security systems, protecting against known threats, offering customizable features, ensuring scalability and performance, and reducing the risk of data breach.
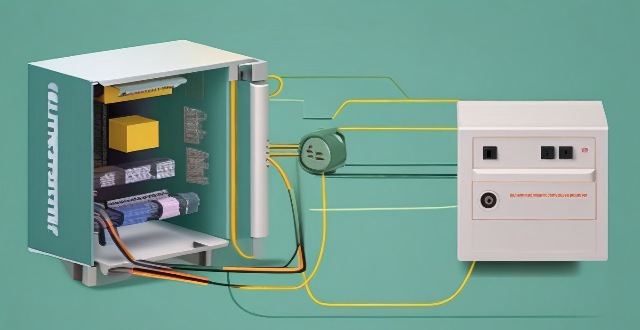
Can you explain the function of a network switch in a home network setup ?
The article discusses the function of a network switch in a home network setup. The primary function of a network switch is to connect multiple devices together, either through Ethernet cables or wireless connections. It also manages data traffic within the network by forwarding data packets to their intended destination based on their IP address. Additionally, network switches enhance network performance by providing dedicated bandwidth to each connected device and prioritizing certain types of traffic over others. Finally, network switches come with various security features that help protect your home network from unauthorized access and cyber threats.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.

Is network expansion necessary for large enterprises ?
In today's digital age, large enterprises rely heavily on their network infrastructure to support their operations. As businesses grow and expand, it becomes increasingly important to ensure that their networks can handle the increased demand. This raises the question: is network expansion necessary for large enterprises? One of the main benefits of network expansion is scalability. As a business grows, its network needs to be able to accommodate the additional users and devices. By expanding the network, businesses can ensure that they have enough bandwidth and resources to support their growing workforce. Network expansion can also improve overall performance. When a network is congested with too many users and devices, it can lead to slower speeds and reduced productivity. By expanding the network, businesses can reduce congestion and improve performance across the board. As businesses grow, they become more attractive targets for cyber attacks. By expanding their network, businesses can implement additional security measures such as firewalls, intrusion detection systems, and access control lists to protect against potential threats. While there are many benefits to network expansion, there are also some challenges that businesses must consider. Expanding a network can be expensive, especially for large enterprises with complex IT infrastructures. Businesses must carefully consider the costs associated with expanding their network, including hardware, software, and maintenance expenses. As networks become larger and more complex, managing them becomes increasingly difficult. Businesses must ensure that they have the necessary expertise and resources to manage their expanded network effectively. When expanding a network, businesses must ensure that all components are compatible with each other. This includes hardware, software, and protocols. Incompatible components can lead to downtime and reduced productivity. To successfully expand a network while minimizing challenges, businesses should follow these best practices: plan ahead, choose the right technology, train personnel, implement security measures, and monitor performance. In conclusion, network expansion is necessary for large enterprises to support their growing operations and maintain high levels of performance and security. However, businesses must carefully consider the challenges associated with expanding their network and follow best practices to minimize these challenges and ensure a successful outcome.

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.

How can I improve my home's Wi-Fi network coverage ?
The text provides tips on how to improve Wi-Fi network coverage at home, including upgrading the router, changing its location, using extenders or mesh networks, updating firmware, adjusting settings, limiting bandwidth-heavy activities, replacing old devices, and using wired connections where possible.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.
What industries will benefit the most from network slicing capabilities ?
The article discusses the concept of network slicing, a technology derived from software-defined networking (SDN) and network function virtualization (NFV), which allows the partitioning of physical networks into multiple virtual networks to optimize resource allocation according to specific service requirements. It outlines the key benefits and applications of network slicing in various sectors such as automotive, healthcare, manufacturing, energy, financial services, and entertainment and media. The conclusion highlights the potential of network slicing to revolutionize communication systems and enhance service delivery, operational efficiency, and user experience across different industries.

What steps can women take to build a strong professional network ?
Building a strong professional network is crucial for career growth and advancement. For women, it can be especially important as they often face unique challenges in the workplace. Here are some steps that women can take to build a robust professional network: 1. Attend industry events and conferences. 2. Join professional organizations and associations. 3. Utilize social media and online platforms. 4. Find a mentor or sponsor. 5. Participate in training programs and workshops. 6. Volunteer for committees or boards. 7. Stay in touch with colleagues and alumni.

How can network slicing be implemented in existing networks ?
Network slicing allows multiple virtual networks to be created from a single physical network, enabling service providers to offer customized services with specific QoS requirements. To implement network slicing in existing networks, assess the current network infrastructure, design the network slices, configure the network devices, and deploy the network slices. This process involves updating device firmware, installing SDN/NFV software, configuring device settings, creating virtual networks, applying QoS policies, and continuously monitoring and optimizing performance.
What are the benefits of using a powerline adapter for home network connectivity ?
Powerline adapters offer a simple and effective way to enhance home network connectivity by using existing electrical wiring. They provide benefits such as ease of installation, stable connections, extended coverage, high performance, and cost-effectiveness.

What are the challenges faced during a network expansion project ?
When expanding a network, organizations may face various challenges that can impact the success of the project. These challenges include budget constraints, technical difficulties, security concerns, downtime and disruptions, training and support requirements, integration with existing systems, regulatory compliance, project management issues, change management, and future-proofing considerations. By proactively addressing these challenges, organizations can successfully complete network expansion projects while minimizing disruptions and maximizing the benefits of the expanded network.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.

What is the purpose of a VPN (Virtual Private Network) device in a business network ?
The purpose of a VPN device in a business network is to provide secure and encrypted connections for remote access to the organization's resources, ensuring that employees, partners, and customers can access the company's data and applications securely from any location. Key features include encryption, authentication, firewall protection, scalability, and flexibility. Benefits of using a VPN device in a business network include enhanced security, improved productivity, cost savings, and simplified IT management.
What strategies can be implemented to optimize wireless network connectivity ?
Optimizing wireless network connectivity is crucial for seamless internet access. Strategies include choosing the right location for the router, updating firmware and drivers, changing the wireless channel, using quality hardware, implementing Quality of Service (QoS) settings, securing the network, and reducing interference from other devices and appliances. These steps can improve wireless network performance and ensure efficient internet access.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.
How do I troubleshoot a faulty network connection device ?
This text provides a step-by-step guide on how to troubleshoot a faulty network connection device. It starts by identifying the problem, checking physical connections, restarting the device, checking network settings, updating firmware, checking for interference, and finally contacting support if all else fails. The text emphasizes the importance of patience and perseverance in troubleshooting technical issues.
How can I improve my home network with Wi-Fi 6 ?
Wi-Fi 6, also known as 802.11ax, is the latest wireless networking standard that promises faster speeds, better range, and improved performance in congested areas. If you're looking to improve your home network with Wi-Fi 6, here are some tips: upgrade your router; place it strategically; use Wi-Fi extenders or mesh networks; and optimize your device settings.
Are there any potential drawbacks or challenges with implementing network slicing ?
Network slicing is a promising technology that allows multiple virtual networks to coexist on a shared physical infrastructure. It enables operators to provide tailored network services for different use cases, such as enhanced mobile broadband (eMBB), ultra-reliable low-latency communications (URLLC), and massive machine-type communications (mMTC). However, there are potential drawbacks and challenges associated with implementing network slicing, including the complexity of management and orchestration, significant infrastructure investment required, standardization and interoperability issues, skill gap within organizations, and regulatory and legal aspects to consider.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.
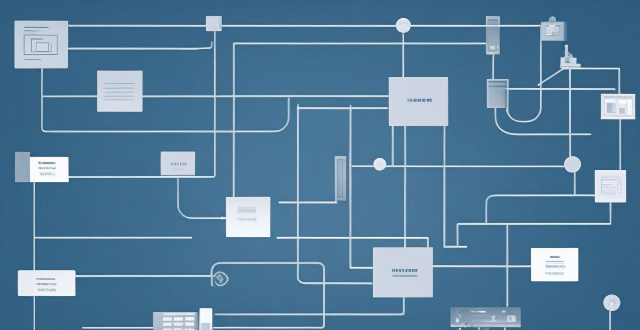
What technology is used in network expansion ?
The text describes various technologies and techniques used in network expansion to increase capacity and coverage, including fiber optics, wireless technologies, software-defined networking (SDN), network function virtualization (NFV), cloud computing, edge computing, network automation and orchestration, multiprotocol label switching (MPLS), cable modems and DSL technology, and submarine cables. Each technology is described in terms of its benefits and how it contributes to network expansion.
What technology is used to extend network coverage in remote locations ?
In remote locations, several technologies are used to extend network coverage, including satellite internet, wireless broadband (Wi-Fi), cellular data, long-range radio networks (LoRaWAN), and fiber optic cables. The choice of technology depends on factors such as cost, availability, and the specific needs of the users in those areas.

How can network coverage be improved in rural areas ?
Improving network coverage in rural areas requires a multi-faceted approach that includes infrastructure development, adoption of advanced technologies, supportive government policies, community participation, and exploration of alternative connectivity solutions. Governments can conduct surveys to assess needs, formulate supportive policies, and allocate budget for rural connectivity. Service providers should invest in R&D, collaborate with other stakeholders, and engage with rural communities to tailor solutions. Local communities should participate in planning, promote digital literacy, and monitor progress.

What are the benefits of having a strong support system for women in managing relationships ?
The article discusses the importance of a strong support system for women in managing relationships. It highlights the benefits of emotional support, advice and guidance, accountability, stress reduction, personal growth, celebration of milestones, and safe space for self-expression that a robust support network provides. The text also suggests ways to cultivate such a support system, including staying connected, being supportive, joining groups, seeking professional help, and ensuring reciprocity in relationships. Overall, the article emphasizes the role of a strong support system in helping women navigate the complexities of personal connections with confidence and resilience.

Is 5G network more secure than 4G ?
The question of whether 5G is more secure than 4G has been a topic of discussion among tech enthusiasts and security experts. While it's true that 5G brings many improvements over its predecessor, including faster speeds and lower latency, the question of security is complex and multifaceted. Let's dive into some key aspects to consider: ## Encryption and Authentication ### Key Points: - **Stronger Encryption**: 5G uses more advanced encryption methods compared to 4G. - **Enhanced Authentication Procedures**: 5G introduces new authentication mechanisms. #### Explanation: 5G networks employ stronger encryption standards than 4G. For instance, it uses algorithms like AES-256 for confidentiality, which is considered very secure. Moreover, 5G includes enhanced authentication procedures such as network function protection and improved identity privacy features. These enhancements make it harder for attackers to intercept or spoof user data. ## Network Slicing and Isolation ### Key Points: - **Network Slicing**: Allows multiple virtual networks on a shared physical infrastructure. - **Improved Isolation**: Helps in containing potential security breaches. #### Explanation: One of the innovative features of 5G is network slicing, which enables operators to create multiple virtual networks tailored for different services or customers. This can improve security by isolating sensitive communications from general traffic, reducing the risk of cross-contamination if one slice gets compromised. ## IoT and Device Density ### Key Points: - **Increased Connectivity**: 5G is designed to support a much higher number of devices. - **Potential Vulnerabilities**: More connected devices could mean more entry points for attacks. #### Explanation: With the rise of IoT (Internet of Things), 5G is expected to connect many more devices than 4G. While this opens up opportunities for smart cities, autonomous vehicles, etc., it also increases the potential attack surface. Each device could be a vulnerability that hackers might exploit. ## Security Standards and Regulations ### Key Points: - **Evolving Standards**: 5G security standards are still evolving. - **International Cooperation**: Global cooperation is essential for setting uniform security regulations. #### Explanation: As with any new technology, the security standards for 5G are still being developed and refined. There's an ongoing effort from international bodies to ensure that 5G networks worldwide adhere to stringent security guidelines. However, the effectiveness of these measures will depend on how consistently they are implemented and enforced across different countries and providers. ## Conclusion In conclusion, while 5G brings several improvements that can enhance security—such as stronger encryption and better authentication mechanisms—it also introduces new challenges due to increased connectivity and the need for global cooperation on security standards. Therefore, it's not straightforward to declare that 5G is inherently more secure than 4G without considering various factors and ongoing developments in both technologies.