Network Malware
How can I protect my network from malware and viruses ?
Malware and viruses can cause significant damage to your network, including data loss, system crashes, and identity theft. To protect your network from these threats, you need to implement a comprehensive security strategy that includes installing antivirus and anti-malware software, using a firewall, keeping your system up-to-date, using strong passwords and 2FA, educating yourself and your employees, and regularly backing up your data. By implementing these steps, you can significantly reduce the risk of malware and virus infections on your network.

Why does my network latency fluctuate throughout the day ?
The article explores various reasons for fluctuations in network latency, including network congestion due to high traffic volume, large file transfers, and server load; physical distance and infrastructure issues related to geographical location, network hardware, and ISP differences; and local network conditions such as wireless interference, multiple devices sharing bandwidth, and malware or viruses affecting performance. It suggests ways to minimize latency fluctuations, like upgrading equipment, optimizing Wi-Fi setup, scheduling large downloads during off-peak hours, using wired connections, and scanning for malware.

What are the most common types of network attacks and how can they be prevented ?
The article outlines the most common types of network attacks and their prevention measures. These include phishing, malware, DoS/DDoS, MitM, SQL injection, XSS, insecure network services, insider threats, password attacks, and wireless network attacks. For each type of attack, the text provides a brief explanation followed by specific prevention strategies. The conclusion emphasizes the importance of a layered security approach that combines education, monitoring, and rapid response to mitigate risks and protect assets.
What are the best tools and technologies for network security protection ?
This article discusses some of the best tools and technologies for network security protection. The list includes firewalls, intrusion detection systems (IDS) and intrusion prevention systems (IPS), virtual private networks (VPNs), antivirus and anti-malware software, next-generation firewalls (NGFWs), network access control (NAC), and security information and event management (SIEM). These tools and technologies can help organizations protect their networks from unauthorized access, data breaches, and other cyber threats. However, it's essential to remember that no single tool or technology can provide complete protection on its own. A layered approach combining multiple solutions is often the most effective way to safeguard your network against today's complex threats.

How do firewalls contribute to network security ?
Firewalls are crucial for network security, offeringFirewalls are crucial for network security, offering, blocking unwanted connections, preventing preventing network intrusion, enforcing security policies, providing VPN support, integrating with other security systems, protecting against known threats, offering customizable features, ensuring scalability and performance, and reducing the risk of data breach.
What are the risks of connecting to a public Wi-Fi network ?
Connecting to a public Wi-Fi network can expose your device and personal information to various risks, including man-in-the-middle attacks, malware distribution, unauthorized access to your device, snooping and data theft, and social engineering attacks. To mitigate these risks, it is recommended to use a Virtual Private Network (VPN) to encrypt your internet traffic, keep your operating system and antivirus software up-to-date, enable your firewall, use websites with HTTPS encryption, verify the authenticity of the Wi-Fi network before connecting, and be cautious about which websites you visit and what information you enter while connected to public Wi-Fi.
How can I protect my home network from cyber attacks ?
The text provides a topic summary on how to protect your home network from cyber attacks. It suggests changing default settings such as passwords and firmware, using strong passwords, securing your Wi-Fi network with WPA2 encryption, keeping devices updated with software patches and antivirus software, and educating yourself and family members about safe online practices. Following these steps can help reduce the risk of cyber attacks and keep personal information secure.

Are there any laws or regulations regarding public Wi-Fi usage ?
Public Wi-Fi usage is governed by laws and regulations related to data protection, copyright infringement, cyberbullying, malware, and privacy policies. It is important to follow best practices for data protection, respect copyright laws, avoid cyberbullying and harassment, protect against malware and viruses, and review privacy policies to stay safe and compliant with the law.

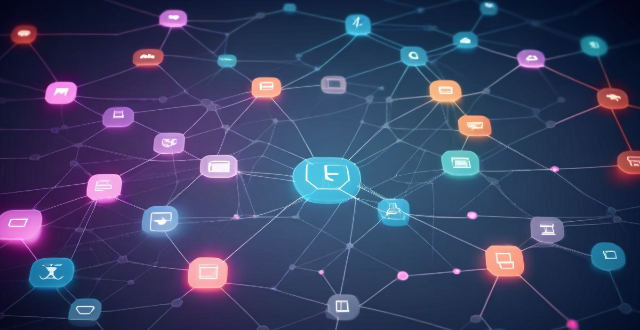
What are the latest trends in network security protection ?
Network security is a crucial aspect of modern computing, and it's constantly evolving to keep up with new threats. Here are some of the latest trends in network security protection: - AI and ML are becoming increasingly popular for detecting and responding to cyber threats. - IoT devices have poor security features or lack them altogether, making them easy targets for hackers. - With more businesses moving to the cloud, ensuring data is secure is essential. - Threat intelligence involves collecting information about potential threats and using it to improve defenses. - The zero trust model assumes that no one should be trusted by default, including those within an organization's network.

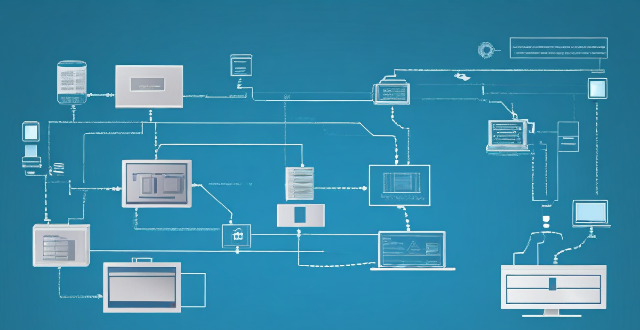
How can I detect and prevent network intrusions ?
To detect and prevent network intrusions, implementTo detect and prevent network intrusions, implement approach that includes: conducting training employees on security best practices, and regularly updating software and firmware. This comprehensive approach can significantly reduce the risk of network intrusions and protect an organization's valuable assets.

What steps can I take to secure my home network ?
Securing your home network is crucial in today's digital age where cyber threats are constantly evolving. Here are some steps you can take to ensure the safety and privacy of your home network: Change default router settings, use strong encryption, set up a guest network, update device software, use firewall and encrypt data, secure your wireless signal, control device access, and monitor network activity. By following these steps, you can significantly enhance the security of your home network and protect your personal information from potential cyber threats.
What is the role of firewalls in network security protection ?
Firewalls are crucial for network security protection, acting as a barrier between trusted and untrusted networks to prevent unauthorized access and block malicious traffic. They monitor network activity for potential threats, with various types including packet-filtering, stateful inspection, application-level, and next-generation firewalls. Firewalls offer benefits such as access control, threat prevention, visibility and auditing, and compliance enforcement. Best practices for deploying firewalls include implementing a multi-layered defense strategy, regularly updating firewall rules and policies, monitoring logs and alerts, conducting regular penetration testing, and training staff on firewall management and maintenance.
How can I improve my internet speed for better network performance ?
To improve internet speed and network performance, consider these steps: check your internet plan; optimize router position; upgrade router or modem; use wired connections; limit bandwidth hogs; scan for malware; update drivers; disable unused apps; clear cache; contact ISP.

Is it safe to use public Wi-Fi networks with my iPhone ?
Using public Wi-Fi networks with your iPhone can be convenient, but it also poses security risks such as unsecured networks, malware attacks, and phishing scams. To stay safe, use a VPN, avoid accessing sensitive information on public networks, keep your device up-to-date, enable two-factor authentication, and be wary of fake hotspots.

How can I ensure my business is protected from cyber threats ?
To ensure your business is protected from cyber threats, consider implementing measures such as educating employees on cybersecurity, using strong passwords and two-factor authentication, keeping software up-to-date, using antivirus and anti-malware software, securing networks with firewalls and encryption, backing up data regularly, limiting access to sensitive information, monitoring network activity, and developing incident response plans.

Can someone hack into my device through public Wi-Fi ?
Public Wi-Fi networks pose a significant risk to the security of your devices due to various types of attacks such as man-in-the-middle, eavesdropping, and malware distribution. To protect yourself from these threats, it is recommended to use a virtual private network (VPN), avoid accessing sensitive information on public Wi-Fi, keep your device up-to-date, use two-factor authentication, and be wary of rogue Wi-Fi networks. Following these tips can significantly reduce the chances of falling victim to hackers and protect your personal information from being stolen or compromised.

What are some common online privacy breaches and how can I prevent them ?
In today's digital age, online privacy breaches are becoming increasingly common. To protect your sensitive data, it is essential to understand the risks involved and take necessary precautions. Some of the most common online privacy breaches include phishing attacks, malware infections, unsecured networks, social engineering tactics, and data breaches. Effective prevention strategies for these breaches include being skeptical of suspicious emails or messages, using anti-phishing tools, regularly updating software, using antivirus software, avoiding suspicious downloads, using virtual private networks (VPNs) on public Wi-Fi networks, securing your home network with strong passwords and encryption settings, educating yourself about social engineering tactics, being cautious with personal information, verifying requests for sensitive information, monitoring your accounts for suspicious activity, using strong passwords, and enabling two-factor authentication. By following these strategies, you can significantly reduce the risk of online privacy breaches and protect your sensitive data from unauthorized access.

Can public Wi-Fi networks be secure ?
Public Wi-Fi networks are convenient but come with security risks. Potential vulnerabilities include unencrypted data transmission, man-in-the-middle attacks, malware distribution, and snooping. To make public Wi-Fi networks more secure, use a VPN, avoid sensitive activities, keep your device up-to-date, use two-factor authentication, and be wary of fake access points.

What are the risks associated with using public Wi-Fi networks ?
Using public Wi-Fi networks can expose you to various risks and vulnerabilities, including Man-in-the-Middle attacks, unencrypted data transmission, malware distribution, phishing scams, insufficient security measures, lack of privacy, session hijacking, and denial of service attacks. To protect yourself from these risks, it is essential to take precautions when using public Wi-Fi networks, such as using a virtual private network (VPN), avoiding sensitive activities like online banking or shopping, and keeping your device's software up-to-date with the latest security patches.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.

What are some common security risks associated with using an iPhone ?
The article discusses common security risks associated with using an iPhone, including unauthorized access, malware attacks, phishing scams, and Wi-Fi networks. To protect against these risks, users should set strong passwords, enable two-factor authentication, avoid suspicious links and downloads, use a VPN when connecting to public Wi-Fi networks, and regularly scan their device for malware. By following these best practices, users can significantly reduce the risk of falling victim to security threats.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

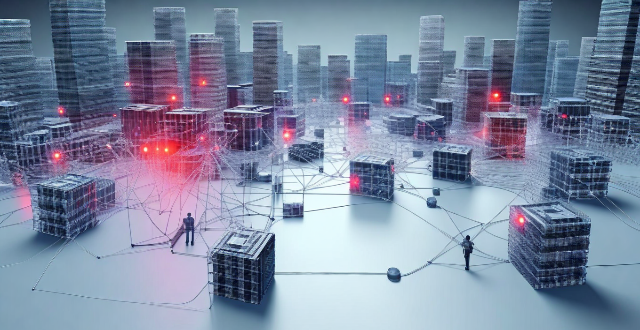
Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

What are the main threats to communication security ?
The text discusses the main threats to communication security, which include eavesdropping and unauthorized access, malware and viruses, social engineering and phishing, insider threats, and DoS attacks. It also provides mitigation strategies for each threat, such as encryption, secure networks, physical security, antivirus software, firewalls, software updates, awareness training, email filters, multi-factor authentication, access controls, monitoring and auditing, termination procedures, rate limiting, content delivery networks (CDNs), and intrusion detection systems (IDS).