Network Risk
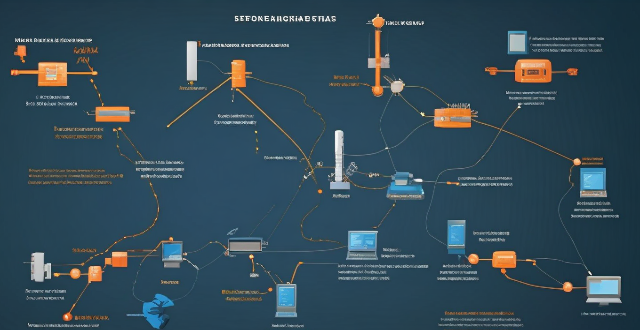
What are the risks of connecting to a public Wi-Fi network ?
Connecting to a public Wi-Fi network can expose your device and personal information to various risks, including man-in-the-middle attacks, malware distribution, unauthorized access to your device, snooping and data theft, and social engineering attacks. To mitigate these risks, it is recommended to use a Virtual Private Network (VPN) to encrypt your internet traffic, keep your operating system and antivirus software up-to-date, enable your firewall, use websites with HTTPS encryption, verify the authenticity of the Wi-Fi network before connecting, and be cautious about which websites you visit and what information you enter while connected to public Wi-Fi.

How can I detect and prevent network intrusions ?
To detect and prevent network intrusions, implementTo detect and prevent network intrusions, implement approach that includes: conducting training employees on security best practices, and regularly updating software and firmware. This comprehensive approach can significantly reduce the risk of network intrusions and protect an organization's valuable assets.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.

How do firewalls contribute to network security ?
Firewalls are crucial for network security, offeringFirewalls are crucial for network security, offering, blocking unwanted connections, preventing preventing network intrusion, enforcing security policies, providing VPN support, integrating with other security systems, protecting against known threats, offering customizable features, ensuring scalability and performance, and reducing the risk of data breach.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.

What are the benefits of network expansion for businesses ?
Network expansion is crucial for business growth, offering benefitsNetwork expansion is crucial for business growth, offering benefits risk diversification, access to access to new opportunities, improved brand awareness, competitive advantage, and enhanced learning.
How can I protect my network from malware and viruses ?
Malware and viruses can cause significant damage to your network, including data loss, system crashes, and identity theft. To protect your network from these threats, you need to implement a comprehensive security strategy that includes installing antivirus and anti-malware software, using a firewall, keeping your system up-to-date, using strong passwords and 2FA, educating yourself and your employees, and regularly backing up your data. By implementing these steps, you can significantly reduce the risk of malware and virus infections on your network.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.
How can I protect my home network from cyber attacks ?
The text provides a topic summary on how to protect your home network from cyber attacks. It suggests changing default settings such as passwords and firmware, using strong passwords, securing your Wi-Fi network with WPA2 encryption, keeping devices updated with software patches and antivirus software, and educating yourself and family members about safe online practices. Following these steps can help reduce the risk of cyber attacks and keep personal information secure.
What is the role of firewalls in network security protection ?
Firewalls are crucial for network security protection, acting as a barrier between trusted and untrusted networks to prevent unauthorized access and block malicious traffic. They monitor network activity for potential threats, with various types including packet-filtering, stateful inspection, application-level, and next-generation firewalls. Firewalls offer benefits such as access control, threat prevention, visibility and auditing, and compliance enforcement. Best practices for deploying firewalls include implementing a multi-layered defense strategy, regularly updating firewall rules and policies, monitoring logs and alerts, conducting regular penetration testing, and training staff on firewall management and maintenance.
Are there any potential drawbacks or challenges with implementing network slicing ?
Network slicing is a promising technology that allows multiple virtual networks to coexist on a shared physical infrastructure. It enables operators to provide tailored network services for different use cases, such as enhanced mobile broadband (eMBB), ultra-reliable low-latency communications (URLLC), and massive machine-type communications (mMTC). However, there are potential drawbacks and challenges associated with implementing network slicing, including the complexity of management and orchestration, significant infrastructure investment required, standardization and interoperability issues, skill gap within organizations, and regulatory and legal aspects to consider.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.

What are the latest trends in network security protection ?
Network security is a crucial aspect of modern computing, and it's constantly evolving to keep up with new threats. Here are some of the latest trends in network security protection: - AI and ML are becoming increasingly popular for detecting and responding to cyber threats. - IoT devices have poor security features or lack them altogether, making them easy targets for hackers. - With more businesses moving to the cloud, ensuring data is secure is essential. - Threat intelligence involves collecting information about potential threats and using it to improve defenses. - The zero trust model assumes that no one should be trusted by default, including those within an organization's network.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

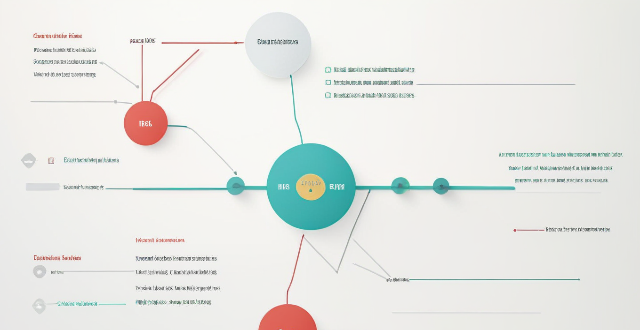
How does network slicing work in 5G technology ?
Network slicing is a feature of 5G technology that allows operators to create multiple virtual networks on a shared physical infrastructure. This enables them to offer customized services with specific quality of service (QoS) and quality of experience (QoE) requirements for different types of customers and applications. The implementation of network slicing involves several key components such as Network Function Virtualization (NFV), Software-Defined Networking (SDN), Network Management and Orchestration (MANO), and Policy Management. The steps involved in implementing network slicing include requirement analysis, resource allocation, virtual network function deployment, resource management, policy enforcement, monitoring and optimization, and lifecycle management. Network slicing offers benefits such as customization, resource efficiency, scalability, improved performance, and enhanced security.

Is 5G network more secure than 4G ?
The question of whether 5G is more secure than 4G has been a topic of discussion among tech enthusiasts and security experts. While it's true that 5G brings many improvements over its predecessor, including faster speeds and lower latency, the question of security is complex and multifaceted. Let's dive into some key aspects to consider: ## Encryption and Authentication ### Key Points: - **Stronger Encryption**: 5G uses more advanced encryption methods compared to 4G. - **Enhanced Authentication Procedures**: 5G introduces new authentication mechanisms. #### Explanation: 5G networks employ stronger encryption standards than 4G. For instance, it uses algorithms like AES-256 for confidentiality, which is considered very secure. Moreover, 5G includes enhanced authentication procedures such as network function protection and improved identity privacy features. These enhancements make it harder for attackers to intercept or spoof user data. ## Network Slicing and Isolation ### Key Points: - **Network Slicing**: Allows multiple virtual networks on a shared physical infrastructure. - **Improved Isolation**: Helps in containing potential security breaches. #### Explanation: One of the innovative features of 5G is network slicing, which enables operators to create multiple virtual networks tailored for different services or customers. This can improve security by isolating sensitive communications from general traffic, reducing the risk of cross-contamination if one slice gets compromised. ## IoT and Device Density ### Key Points: - **Increased Connectivity**: 5G is designed to support a much higher number of devices. - **Potential Vulnerabilities**: More connected devices could mean more entry points for attacks. #### Explanation: With the rise of IoT (Internet of Things), 5G is expected to connect many more devices than 4G. While this opens up opportunities for smart cities, autonomous vehicles, etc., it also increases the potential attack surface. Each device could be a vulnerability that hackers might exploit. ## Security Standards and Regulations ### Key Points: - **Evolving Standards**: 5G security standards are still evolving. - **International Cooperation**: Global cooperation is essential for setting uniform security regulations. #### Explanation: As with any new technology, the security standards for 5G are still being developed and refined. There's an ongoing effort from international bodies to ensure that 5G networks worldwide adhere to stringent security guidelines. However, the effectiveness of these measures will depend on how consistently they are implemented and enforced across different countries and providers. ## Conclusion In conclusion, while 5G brings several improvements that can enhance security—such as stronger encryption and better authentication mechanisms—it also introduces new challenges due to increased connectivity and the need for global cooperation on security standards. Therefore, it's not straightforward to declare that 5G is inherently more secure than 4G without considering various factors and ongoing developments in both technologies.

How can I create a strong password policy for my network ?
Creating a strong password policy is crucial for the security of your network. Follow these steps to create an effective password policy: 1. Determine the purpose of the password policy. 2. Define password requirements. 3. Enforce password changes. 4. Store passwords securely. 5. Train users on password security. 6. Monitor and audit password use.

Is network slicing secure for sensitive data transmission ?
Network slicing is a technology that allows multiple virtual networks to coexist on a shared physical infrastructure, enabling service providers to offer customized services with different QoS requirements. While network slicing offers numerous benefits such as customization, resource allocation, scalability, and isolation, there are also potential security concerns that need to be addressed. These include data isolation, access control, encryption, and intrusion detection and prevention systems (IDPS). By implementing robust isolation mechanisms, access control policies, strong encryption algorithms, and effective IDPS, service providers can leverage network slicing while maintaining the security of sensitive data transmission.
What technology is used to extend network coverage in remote locations ?
In remote locations, several technologies are used to extend network coverage, including satellite internet, wireless broadband (Wi-Fi), cellular data, long-range radio networks (LoRaWAN), and fiber optic cables. The choice of technology depends on factors such as cost, availability, and the specific needs of the users in those areas.

What are the most common types of network attacks and how can they be prevented ?
The article outlines the most common types of network attacks and their prevention measures. These include phishing, malware, DoS/DDoS, MitM, SQL injection, XSS, insecure network services, insider threats, password attacks, and wireless network attacks. For each type of attack, the text provides a brief explanation followed by specific prevention strategies. The conclusion emphasizes the importance of a layered security approach that combines education, monitoring, and rapid response to mitigate risks and protect assets.
What role does caching play in network optimization ?
Caching is crucial for network optimization, improving dataCaching is crucial for network optimization, improving data speed by storing frequently accessed data improving data retrieval performance and speed by storing frequently accessed data in temporary storage areas. It reduces latency, decreases bandwidth usage, improves scalability, enhances resilience, optimizes content delivery, reduces server load, improves data consistency, and increases availability. These benefits make caching essential for improving network infrastructure performance and reliability.

What are the best practices for network security protection ?
The text provides a detailed outline on the best practices for network security protection, which can be summarized in the following points: 1. **Use Strong Passwords**: Create complex passwords using a mix of characters and numbers, change them regularly, avoid personal information, and use a password manager. 2. **Keep Software Up-to-date**: Regularly update all software to patch vulnerabilities and enable automatic updates where possible. 3. **Implement Firewall Protection**: Use both hardware and software firewalls, configure rules to allow necessary traffic only, and monitor firewall logs. 4. **Use Encryption**: Encrypt sensitive data in transit and at rest, use VPNs for remote connections, and implement end-to-end encryption for high-security communications. 5. **Educate Employees on Security Best Practices**: Conduct regular training, encourage safe online behavior, and establish clear policies for device and internet use. 6. **Limit Access Rights**: Grant access based on need, review and revoke unnecessary rights, and use multi-factor authentication for sensitive resources. 7. **Backup Data Regularly**: Create regular backups, test them periodically, and implement version control for important files. 8. **Monitor Network Activity**: Use IDS and IPS systems, set up alerts for unusual activity, and conduct regular security audits. By adhering to these practices, organizations can significantly enhance their network security posture and mitigate the risks associated with cyber threats.
Can network slicing improve internet speed and reliability ?
Network slicing is a concept that divides a physical network into multiple virtual networks, each optimized for a specific use case. This approach can improve internet speed and reliability by enabling efficient resource allocation, enhancing performance through customization and optimization, and improving reliability through isolation and scalability. However, effective implementation requires careful planning and coordination among stakeholders involved in the network infrastructure.

How long does it take to complete a network expansion project ?
Completing a network expansion project involves several stages, including planning and design, procurement, installation and configuration, testing and troubleshooting, and deployment and training. The duration of each stage can vary depending on factors such as project size, resource availability, and team efficiency. A general timeline for completing a network expansion project is 6 months to a year.
What are the best tools and technologies for network security protection ?
This article discusses some of the best tools and technologies for network security protection. The list includes firewalls, intrusion detection systems (IDS) and intrusion prevention systems (IPS), virtual private networks (VPNs), antivirus and anti-malware software, next-generation firewalls (NGFWs), network access control (NAC), and security information and event management (SIEM). These tools and technologies can help organizations protect their networks from unauthorized access, data breaches, and other cyber threats. However, it's essential to remember that no single tool or technology can provide complete protection on its own. A layered approach combining multiple solutions is often the most effective way to safeguard your network against today's complex threats.
How does network congestion impact latency ?
The impact of network congestion on latency can be significant and can have a negative effect on the overall performance of the network. This can include increased transmission time, higher drop rates, reduced bandwidth availability, and impacts on application performance. It is important for network administrators to monitor and manage network traffic to minimize the impact of congestion on latency and ensure that applications continue to function properly.