Network Connectivity
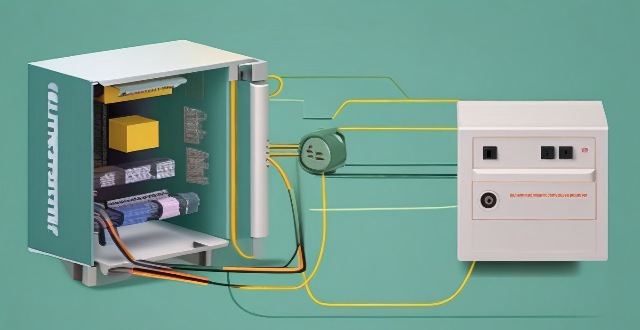
What are the benefits of using a powerline adapter for home network connectivity ?
Powerline adapters offer a simple and effective way to enhance home network connectivity by using existing electrical wiring. They provide benefits such as ease of installation, stable connections, extended coverage, high performance, and cost-effectiveness.

How often should I replace my network connectivity devices to maintain optimal performance ?
### **How Often Should I Replace My Network Connectivity Devices to Maintain Optimal Performance?** Maintaining optimal performance in your network connectivity devices is essential for seamless internet activities. The frequency of replacement depends on factors like the device's age, performance issues, compatibility with other devices, and future-proofing considerations. Most network devices have an expected lifespan of 3-5 years, but technology advances rapidly, offering improvements in speed, security, and features. Performance issues like slow speeds and frequent disconnections can indicate the need for replacement. Compatibility with newer tech and security standards is also crucial. Future-proofing by investing in the latest technology and scalable devices ensures longevity. Regular maintenance, monitoring performance through speed tests and user reviews, and strategic upgrading can help maximize the lifespan of your network equipment and ensure optimal performance.

How does a network bridge improve internet connectivity ?
A network bridge is a device that connects two or more networks at the data link layer, offering benefits such as reduced congestion, increased security, enhanced performance, cost-effectiveness, and compatibility. It improves internet connectivity by segregating traffic, filtering based on MAC addresses, optimizing routing, and extending the use of existing infrastructure. Bridges are applicable in home, enterprise, and public access networks for connecting devices, separating departmental networks, and providing guest access.
What strategies can be implemented to optimize wireless network connectivity ?
Optimizing wireless network connectivity is crucial for seamless internet access. Strategies include choosing the right location for the router, updating firmware and drivers, changing the wireless channel, using quality hardware, implementing Quality of Service (QoS) settings, securing the network, and reducing interference from other devices and appliances. These steps can improve wireless network performance and ensure efficient internet access.

What are the most common types of network connectivity devices ?
This text discusses the various types of network connectivity devices, including routers, switches, modems, and wireless access points. Routers are used to forward data packets between computer networks, while switches are used to connect devices within a network. Modems convert digital data to analog signals for transmission over communication channels, and wireless access points allow wireless devices to connect to a wired network. The features of each device are also discussed, such as routing decisions, data transmission, security, and error detection and correction.
What is the difference between a router and a modem in network connectivity ?
The text delineates the differences between a router and a modem, highlighting their distinct roles within a network. A modem primarily converts digital signals to analog for transmission over telephone lines or cables, while a router creates a local area network (LAN) that enables multiple devices to connect and communicate with each other and the internet. Combination devices that integrate both functionalities are also discussed, noting their convenience but potential lack of advanced features compared to separate units. Understanding these differences is crucial for setting up and maintaining a reliable internet connection.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.

Can you recommend an affordable network connectivity device for a small business ?
Recommendation for an Affordable Network Connectivity Device for a Small Business: TP-Link Archer AX10, which offers Wi-Fi 6 support, MU-MIMO technology, Beamforming technology, Gigabit Ethernet ports, and security features.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.
Can existing devices support 5G network ?
This article discusses whether existing devices can support 5G network and what factors influence this compatibility. The most important factor determining whether a device can support 5G is its hardware, including the modem, antenna, and other components required for 5G connectivity. Another factor that can affect compatibility is the software on your device, such as an outdated operating system or lack of necessary drivers and firmware updates. Finally, even if your device has the necessary hardware and software, you still need to have a carrier that supports 5G in your area. To check if your device is compatible with 5G, you can check your device's specifications, ensure that it is running the latest operating system and has all necessary drivers and firmware updates installed, contact your carrier to see if they offer 5G service in your area and if your plan includes access to this network, and consult with a professional or contact the manufacturer for assistance.
What is 5G network and how does it work ?
The 5G network is the fifth generation of mobile networks, offering significant improvements in speed, capacity, and responsiveness over its predecessor, 4G. It utilizes higher frequencies, advanced antenna technology, and reduced latency to provide enhanced mobile broadband, lower latency, increased reliability, massive IoT connectivity, and improved energy efficiency. The rollout of 5G worldwide is expected to enable new applications and services that were not possible with previous network technologies.

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.
What technology is used in network expansion ?
The text describes various technologies and techniques used in network expansion to increase capacity and coverage, including fiber optics, wireless technologies, software-defined networking (SDN), network function virtualization (NFV), cloud computing, edge computing, network automation and orchestration, multiprotocol label switching (MPLS), cable modems and DSL technology, and submarine cables. Each technology is described in terms of its benefits and how it contributes to network expansion.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

What are the best practices for mobile network optimization ?
The article provides best practices for mobile network optimization, which are crucial for ensuring seamless connectivity and efficient data transfer. The practices include proper site selection, cell configuration, spectrum allocation, power control, antenna selection, frequency reuse, load balancing, congestion control, QoS, regular maintenance, fault detection and resolution, performance monitoring, authentication and authorization, encryption, and intrusion detection and prevention. By following these practices, mobile network operators can optimize their networks for better performance, reliability, and security, ultimately providing a better user experience for their customers.

Is 5G network more secure than 4G ?
The question of whether 5G is more secure than 4G has been a topic of discussion among tech enthusiasts and security experts. While it's true that 5G brings many improvements over its predecessor, including faster speeds and lower latency, the question of security is complex and multifaceted. Let's dive into some key aspects to consider: ## Encryption and Authentication ### Key Points: - **Stronger Encryption**: 5G uses more advanced encryption methods compared to 4G. - **Enhanced Authentication Procedures**: 5G introduces new authentication mechanisms. #### Explanation: 5G networks employ stronger encryption standards than 4G. For instance, it uses algorithms like AES-256 for confidentiality, which is considered very secure. Moreover, 5G includes enhanced authentication procedures such as network function protection and improved identity privacy features. These enhancements make it harder for attackers to intercept or spoof user data. ## Network Slicing and Isolation ### Key Points: - **Network Slicing**: Allows multiple virtual networks on a shared physical infrastructure. - **Improved Isolation**: Helps in containing potential security breaches. #### Explanation: One of the innovative features of 5G is network slicing, which enables operators to create multiple virtual networks tailored for different services or customers. This can improve security by isolating sensitive communications from general traffic, reducing the risk of cross-contamination if one slice gets compromised. ## IoT and Device Density ### Key Points: - **Increased Connectivity**: 5G is designed to support a much higher number of devices. - **Potential Vulnerabilities**: More connected devices could mean more entry points for attacks. #### Explanation: With the rise of IoT (Internet of Things), 5G is expected to connect many more devices than 4G. While this opens up opportunities for smart cities, autonomous vehicles, etc., it also increases the potential attack surface. Each device could be a vulnerability that hackers might exploit. ## Security Standards and Regulations ### Key Points: - **Evolving Standards**: 5G security standards are still evolving. - **International Cooperation**: Global cooperation is essential for setting uniform security regulations. #### Explanation: As with any new technology, the security standards for 5G are still being developed and refined. There's an ongoing effort from international bodies to ensure that 5G networks worldwide adhere to stringent security guidelines. However, the effectiveness of these measures will depend on how consistently they are implemented and enforced across different countries and providers. ## Conclusion In conclusion, while 5G brings several improvements that can enhance security—such as stronger encryption and better authentication mechanisms—it also introduces new challenges due to increased connectivity and the need for global cooperation on security standards. Therefore, it's not straightforward to declare that 5G is inherently more secure than 4G without considering various factors and ongoing developments in both technologies.
What is the importance of having a good network coverage ?
The text discusses the importance of having a good network coverage in today's world where communication and connectivity are essential aspects of our daily lives. It outlines several reasons why having a strong and reliable network coverage is crucial, including improved communication, better access to information, enhanced productivity, entertainment on the go, safety and security, and business growth and opportunities. The text concludes that having a good network coverage is an integral part of our modern lifestyle and should not be overlooked when choosing a service provider or planning internet usage.
How do I troubleshoot a faulty network connection device ?
This text provides a step-by-step guide on how to troubleshoot a faulty network connection device. It starts by identifying the problem, checking physical connections, restarting the device, checking network settings, updating firmware, checking for interference, and finally contacting support if all else fails. The text emphasizes the importance of patience and perseverance in troubleshooting technical issues.
Can network slicing improve internet speed and reliability ?
Network slicing is a concept that divides a physical network into multiple virtual networks, each optimized for a specific use case. This approach can improve internet speed and reliability by enabling efficient resource allocation, enhancing performance through customization and optimization, and improving reliability through isolation and scalability. However, effective implementation requires careful planning and coordination among stakeholders involved in the network infrastructure.
How can I improve my home network with Wi-Fi 6 ?
Wi-Fi 6, also known as 802.11ax, is the latest wireless networking standard that promises faster speeds, better range, and improved performance in congested areas. If you're looking to improve your home network with Wi-Fi 6, here are some tips: upgrade your router; place it strategically; use Wi-Fi extenders or mesh networks; and optimize your device settings.

How does network coverage vary between different mobile carriers ?
Network coverage among mobile carriers varies due to differences in infrastructure investments, partnerships and roaming agreements, and technological advancements. Carriers that invest heavily in building and maintaining their network infrastructure are likely to have more extensive coverage than those with limited resources. Partnerships and roaming agreements allow customers to use the partner network's services in areas where the original carrier does not have coverage. Technological advancements like 5G promise faster speeds and better coverage, especially in densely populated urban areas. The geographic coverage of mobile carriers varies significantly, with some carriers focusing on providing extensive coverage across large regions while others prioritize dense urban areas. Speed and capacity also differ among carriers, with those having more advanced infrastructure and technologies typically offering higher speeds and greater capacity. Quality of service is another factor that varies among mobile carriers, including aspects such as call clarity, connection reliability, and data transfer rates. Customers should consider these factors when choosing a carrier to ensure reliable and efficient mobile connectivity.
What industries will benefit the most from network slicing capabilities ?
The article discusses the concept of network slicing, a technology derived from software-defined networking (SDN) and network function virtualization (NFV), which allows the partitioning of physical networks into multiple virtual networks to optimize resource allocation according to specific service requirements. It outlines the key benefits and applications of network slicing in various sectors such as automotive, healthcare, manufacturing, energy, financial services, and entertainment and media. The conclusion highlights the potential of network slicing to revolutionize communication systems and enhance service delivery, operational efficiency, and user experience across different industries.

What is the purpose of a VPN (Virtual Private Network) device in a business network ?
The purpose of a VPN device in a business network is to provide secure and encrypted connections for remote access to the organization's resources, ensuring that employees, partners, and customers can access the company's data and applications securely from any location. Key features include encryption, authentication, firewall protection, scalability, and flexibility. Benefits of using a VPN device in a business network include enhanced security, improved productivity, cost savings, and simplified IT management.
Can you explain the function of a network switch in a home network setup ?
The article discusses the function of a network switch in a home network setup. The primary function of a network switch is to connect multiple devices together, either through Ethernet cables or wireless connections. It also manages data traffic within the network by forwarding data packets to their intended destination based on their IP address. Additionally, network switches enhance network performance by providing dedicated bandwidth to each connected device and prioritizing certain types of traffic over others. Finally, network switches come with various security features that help protect your home network from unauthorized access and cyber threats.

How fast is the 5G network compared to 4G ?
The fifth generation of wireless systems (5G) is significantly faster than the fourth generation (4G). The speeds achievable with 5G can vary depending on several factors, including network congestion, device capabilities, and the specific technology implementation. However, here are some general comparisons to give you an idea of the differences: - Download Speeds: Typical download speeds for 4G can range from 10 to 50 Mbps (Megabits per second), while with 5G, download speeds can start around 100 Mbps and can go up to multiple Gbps (Gigabits per second), with peak theoretical speeds reaching as high as 20 Gbps. - Latency: Latency in 4G networks typically falls between 30 to 50 milliseconds, while one of the major improvements with 5G is its reduced latency, which can be as low as 1 millisecond. - Bandwidth and Capacity: While 4G offers sufficient bandwidth for many current applications, it can struggle under heavy loads or during high-traffic events, while 5G is designed to handle much higher capacity and density of connections, making it better suited for crowded areas and large-scale deployments. With faster speeds and lower latency, streaming services can offer higher resolutions with less buffering, meaning smoother playback for 4K and even 8K video content. 5G's low latency makes it ideal for Augmented Reality (AR) and Virtual Reality (VR) experiences that require real-time interactions without delays. 5G can connect many more devices simultaneously than 4G, facilitating the growth of smart cities, autonomous vehicles, and other IoT applications. Improved network reliability and coverage mean fewer dropped calls and better performance in rural or remote areas. In summary, while 4G has been a transformative technology that has enabled mobile internet access on a large scale, 5G promises to take connectivity to the next level with speeds that are potentially dozens of times faster and latency that is nearly imperceptible. These advancements open up new possibilities for various industries and technologies that were not feasible with 4G.

How does network expansion impact customer experience ?
Network expansion improves customer experience by increasing coverage, reducing disconnections, boosting speed and reliability, and enhancing accessibility to services and devices.
How much does it cost to upgrade to 5G network ?
The cost of upgrading to a 5G network varies depending on several factors, including your current plan, the carrier you are using, and the device you have. If you want to take advantage of 5G speeds, you will need a 5G-compatible device which can range from $200 to over $1000. The cost of upgrading to a 5G plan also depends on your carrier, with some offering unlimited data plans starting at around $70 per month. In addition to a new device and plan, you may also need to purchase accessories such as cases or screen protectors that are compatible with your new device. Finally, if you are installing a 5G network in your home or office, there may be additional costs associated with installation fees or equipment rental fees.

What is the role of bandwidth management in network optimization ?
Bandwidth management is a critical component of network optimization, as it involves controlling and managing the amount of data that can be transmitted over a network at any given time. By effectively managing bandwidth, network administrators can ensure optimal performance and prevent congestion, leading to faster speeds and improved overall network efficiency. Key benefits of bandwidth management include improved network performance, reduced congestion, enhanced user experience, cost savings, and increased security. Techniques for effective bandwidth management include Quality of Service (QoS), traffic shaping, caching, compression, and load balancing. Best practices for bandwidth management involve monitoring network usage, implementing policies and guidelines, using QoS settings appropriately, updating hardware and software regularly, and educating users about proper network usage.

Why do some areas have poor network coverage ?
Poor network coverage is a multifaceted issue influenced by geography, economics, technology, regulation, and environmental factors. Addressing these challenges requires a collaborative effort from governments, private sectors, and communities to ensure that connectivity is accessible to all, regardless of their location.

How can network coverage be improved in rural areas ?
Improving network coverage in rural areas requires a multi-faceted approach that includes infrastructure development, adoption of advanced technologies, supportive government policies, community participation, and exploration of alternative connectivity solutions. Governments can conduct surveys to assess needs, formulate supportive policies, and allocate budget for rural connectivity. Service providers should invest in R&D, collaborate with other stakeholders, and engage with rural communities to tailor solutions. Local communities should participate in planning, promote digital literacy, and monitor progress.