Device Discuss

How do I choose a car charger for my device ?
When selecting a car charger for your device, consider factors such as compatibility with your device's charging port, charging speed, number of ports, additional features, reviews and ratings, budget, and brand reputation. By doing so, you can find a reliable and efficient car charger that meets your needs.
How do I troubleshoot a faulty network connection device ?
This text provides a step-by-step guide on how to troubleshoot a faulty network connection device. It starts by identifying the problem, checking physical connections, restarting the device, checking network settings, updating firmware, checking for interference, and finally contacting support if all else fails. The text emphasizes the importance of patience and perseverance in troubleshooting technical issues.

Can I use Apple Music without an Apple device ?
The text discusses the availability of Apple Music across various platforms, including Windows, Android devices, web players, and smart TVs and streaming devices. It highlights the key features available on each platform and concludes that users don't need an Apple device to enjoy Apple Music.

How do I set up parental controls on my child's Apple device ?
The text provides a step-by-step guide on how to set up parental controls on an Apple device for children. The steps include creating a family group, turning on Screen Time, setting up content and privacy restrictions, establishing downtime and app limits, and monitoring the child's device usage. The purpose of these steps is to ensure the child's safety and well-being while using technology by controlling what apps, websites, and features they can access, as well as when and how much they can use their device.

How to use "Find My iPhone" to locate a missing device ?
The text provides a step-by-step guide on how to use the "Find My iPhone" feature to locate a missing Apple device. It emphasizes the importance of enabling the feature beforehand, signing in to iCloud, selecting the correct device, viewing its location on a map, and using additional features such as marking it as lost or erasing data remotely. It also suggests contacting local authorities if the device is believed to be stolen. Overall, it highlights the effectiveness of "Find My iPhone" in locating lost devices and protecting personal information.

How do I remove a device from my Apple account ?
Removing a device from your Apple account is a straightforward process that can be done in just a few steps. First, sign in to your Apple ID account page by going to [appleid.apple.com](https://appleid.apple.com) and entering your Apple ID and password. Then, view your devices by clicking on the "Devices" section. Choose the device you want to remove from the list of associated devices and click on it. To remove the device from your account, click on the "Remove" button. Confirm the removal in the pop-up window that appears. Finally, check your email for a confirmation message from Apple. Remember that removing a device from your account does not delete any data stored on the device itself; it only removes access to your Apple services such as iCloud and the App Store.

Can someone hack into my device through public Wi-Fi ?
Public Wi-Fi networks pose a significant risk to the security of your devices due to various types of attacks such as man-in-the-middle, eavesdropping, and malware distribution. To protect yourself from these threats, it is recommended to use a virtual private network (VPN), avoid accessing sensitive information on public Wi-Fi, keep your device up-to-date, use two-factor authentication, and be wary of rogue Wi-Fi networks. Following these tips can significantly reduce the chances of falling victim to hackers and protect your personal information from being stolen or compromised.

How do I know if a second-hand electronic device is still functional ?
Before buying a second-hand electronic device, it's important to check its functionality. Here are some steps you can take: visual inspection for physical damage, powering up the device, testing basic functions, checking battery life, connectivity tests, camera and microphone test, speaker and sound quality check, app testing, heat test, and resetting the device. By following these steps, you can make an informed decision about your purchase.
Is there a way to disable automatic updates in my Apple device ?
How to disable automatic updates in Apple device?

What are the benefits of using a GPS device for cycling routes ?
Using a GPS device for cycling routes offers benefits such as improved navigation, safety and security, performance tracking, and convenience. It provides accurate directions, real-time tracking, and the ability to save points of interest. Safety features include emergency alerts, night riding capabilities, and weather updates. Performance tracking measures speed, distance, elevation gain, and heart rate. Convenience is enhanced with no need for paper maps and automatic routing. Overall, using a GPS device can greatly enhance the cycling experience.

**How often does iCloud back up my device, and can I control when it happens ?
iCloud backup is a feature that automatically backs up iOS devices to Apple's cloud storage service, ensuring data safety and restoration if needed. The frequency of these automatic backups depends on available iCloud space and device usage, typically occurring daily under specific conditions like Wi-Fi connection and device lock. Users can control when iCloud backup happens by manually initiating backups, turning off automatic backups, or adjusting backup settings.

How do I optimize my network connection device for video conferencing ?
Optimizing your network connection device for video conferencing is essential for a smooth and reliable communication experience. Here are some steps to follow: 1. Check Your Internet Speed: Test your connection speed and upgrade your plan if necessary. 2. Choose the Right Hardware: Use a wired Ethernet connection if possible, and ensure that your router and modem are up-to-date. 3. Optimize Your Network Settings: Set up Quality of Service (QoS) on your router and keep its firmware updated. 4. Minimize Interference: Reduce wireless interference and limit bandwidth usage during important video calls. 5. Use a Dedicated Network for Video Conferencing: Create a separate Virtual Private Network (VPN) or invest in business-grade networking solutions. By following these steps, you can optimize your network connection device for video conferencing, ensuring smooth and reliable communication with colleagues and clients around the world.

What is the purpose of a VPN (Virtual Private Network) device in a business network ?
The purpose of a VPN device in a business network is to provide secure and encrypted connections for remote access to the organization's resources, ensuring that employees, partners, and customers can access the company's data and applications securely from any location. Key features include encryption, authentication, firewall protection, scalability, and flexibility. Benefits of using a VPN device in a business network include enhanced security, improved productivity, cost savings, and simplified IT management.
**How can I access and manage my iCloud data from a non-Apple device ?
This guide provides step-by-step instructions on how to access and manage iCloud data from a non-Apple device. It includes prerequisites such as having an active iCloud account and using a compatible web browser. The steps include visiting the iCloud website, logging in to your account, choosing a service to access, managing your data, and signing out of iCloud when finished. Common actions within each service are also outlined. By following these steps, users can effectively access and manage their iCloud data from any non-Apple device with an internet connection and a compatible web browser.

How do I set up a VPN service on my computer or mobile device ?
Setting up a VPN (Virtual Private Network) is an excellent way to ensure your online privacy, bypass geo-restrictions, and enhance your security on the internet. Here's a detailed guide to setting up a VPN service on your computer or mobile device: 1. Choose a VPN Service Provider: Research and select a reliable VPN service that suits your needs in terms of security, speed, and price. Ensure the provider offers apps for your operating system, whether it's Windows, macOS, Android, or iOS. 2. Sign Up for the Service: Visit the VPN service website and sign up for an account. Choose a payment plan and complete the subscription process. 3. Download and Install the VPN App: Once you have subscribed, download the VPN app from your provider's website or your device's app store. Install the app on your device following the standard installation procedures. 4. Configure the VPN App: Open the VPN app and log in using your account credentials. Select a server location; usually, the app will recommend the fastest or closest server to you. Customize the settings if needed, such as enabling startup with Windows or configuring the kill switch feature. 5. Connect to the VPN: Click the connect button in the VPN app to establish a connection to the chosen server. A secure and encrypted tunnel will be created between your device and the server. 6. Verify the VPN Connection: Check your IP address and location using online services like `ipleak.net` to ensure your real identity is concealed. Test the connection by trying to access content that is normally blocked in your region. 7. Troubleshooting: If you encounter connection issues, check your network settings or try connecting to a different server. Make sure your firewall and antivirus software are not blocking the VPN connection. 8. Regular Maintenance and Updates: Keep your VPN app updated to benefit from the latest security features and performance improvements. Monitor your data usage if your VPN service has bandwidth limitations. Additional Considerations: Look for VPN services that offer strong encryption protocols like OpenVPN or IKEv2 for maximum security. Ensure that your VPN service has a strict no-logs policy to protect your online activities from being recorded. Some VPN services allow multiple devices to be connected simultaneously under one account – consider this feature if you use multiple devices.

What are the most common types of network connectivity devices ?
This text discusses the various types of network connectivity devices, including routers, switches, modems, and wireless access points. Routers are used to forward data packets between computer networks, while switches are used to connect devices within a network. Modems convert digital data to analog signals for transmission over communication channels, and wireless access points allow wireless devices to connect to a wired network. The features of each device are also discussed, such as routing decisions, data transmission, security, and error detection and correction.
How does Wi-Fi 6 handle multiple device connections at once ?
Wi-Fi 6, the latest wireless networking standard, is designed to handle multiple device connections at once through techniques such as OFDMA, MU-MIMO, BSS coloring, and TWT. These features improve network efficiency, increase speed and performance, extend battery life, reduce interference, and provide greater scalability for growing networks.

**How long does it typically take for iCloud to complete a full backup ?
iCloud backup time varies based on data amount, internet speed, device performance, and server issues. Small backups may take 1-2 hours, moderate ones several hours, and large ones several days. Tips to improve backup times include connecting to Wi-Fi, closing unused apps, updating the device, checking internet connection, and contacting Apple Support if needed.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

Is Apple Music available on Android devices ?
Apple Music is a popular music streaming service by Apple Inc., and it's not exclusive to iOS devices. It's also available for Android users. The availability of Apple Music on Android devices allows users to download the app from the Google Play Store and enjoy all the features that come with a subscription. To download the Apple Music app on an Android device, users need to open the Google Play Store app, search for "Apple Music" in the search bar, select the official Apple Music app from the search results, and click on the "Install" button to download and install the app on their device. Once downloaded and installed, users can start using the app right away and enjoy features such as music streaming, radio stations, playlists, sync across devices, and offline listening.

How do I safely dispose of old or damaged electrical devices ?
This comprehensive guide outlines steps for safely disposing of old or damaged electrical devices, including identifying the type of device, checking with the manufacturer, contacting local authorities and recycling centers, donating or selling still-functional devices, properly packaging and transporting devices, considering environmental impacts, and avoiding harmful disposal methods.

Can I downgrade to a previous version of iOS after updating ?
Downgrading to a previous version of iOS is possible but involves backing up your device, downloading the older firmware, putting your device into recovery mode, restoring through iTunes or Finder, and setting up your device again. Reasons for downgrading include compatibility issues, performance concerns, bugs, and personal preference. However, there are risks such as data loss and security vulnerabilities, and Apple's signing window limits the versions you can downgrade to. It's generally recommended to stay on the latest iOS for the best experience and support.
How much does it cost to upgrade to 5G network ?
The cost of upgrading to a 5G network varies depending on several factors, including your current plan, the carrier you are using, and the device you have. If you want to take advantage of 5G speeds, you will need a 5G-compatible device which can range from $200 to over $1000. The cost of upgrading to a 5G plan also depends on your carrier, with some offering unlimited data plans starting at around $70 per month. In addition to a new device and plan, you may also need to purchase accessories such as cases or screen protectors that are compatible with your new device. Finally, if you are installing a 5G network in your home or office, there may be additional costs associated with installation fees or equipment rental fees.

How will Wi-Fi 6 impact battery life on my devices ?
Wi-Fi 6, the latest wireless networking standard, has the potential to significantly impact device battery life. Key features such as higher data rates, improved network efficiency, and Target Wake Time (TWT) contribute to reduced energy consumption and extended battery life on devices. Faster data rates allow for quicker task completion, while improved network efficiency reduces communication attempts in crowded environments. The TWT feature enables devices to schedule communication with the access point, reducing unnecessary background activity and saving power. Overall, Wi-Fi 6 can help extend the battery life of smartphones, laptops, tablets, and other connected devices by improving network performance and reducing energy usage.

What are the security concerns related to IoT ?
The article discusses the major security concerns related to the Internet of Things (IoT), such as data privacy and confidentiality, device security, network security, physical security, and software vulnerabilities. It emphasizes the need for implementing appropriate security measures to ensure the secure deployment of IoT devices and protect sensitive information from unauthorized access.

How do I manage storage space on my Apple device ?
Managing Storage Space on Your Apple Device Checking Storage Space: - Open Settings and tap General. - Select iPhone Storage (or iPad/iPod Storage). - View a bar graph showing used and available storage, and a list of apps sorted by storage usage. Tips for Managing Storage Space: 1. Delete Unused Apps: Remove apps from the Home Screen or through Settings to free up space. 2. Offload Unused Apps: Enable Offload Unused Apps in Settings to remove apps while keeping their data. 3. Optimize Photo Storage: Use Optimized Storage in Photos settings and manually delete unwanted photos/videos. 4. Clear App Cache and Data: Offload apps to keep their data and reinstall them to remove it. 5. Use Cloud Services: Back up to iCloud and store files in iCloud Drive to save local storage. 6. Manage Messages: Auto-delete old messages and review attachments before deleting conversations. 7. Manage Media and Downloads: Stream content instead of downloading and delete downloaded episodes and songs. 8. Other Tips: Regularly check storage, disable auto downloads, and consider resetting your device if needed.

How can I make sure my GPS is updated for a cross-country road trip ?
To prepare for a cross-country road trip, it's essential to ensure your GPS is up-to-date. Here are the key steps: 1. **Check Compatibility**: Ensure your device can receive updates. 2. **Connect to the Internet**: Use a reliable connection for downloading updates. 3. **Visit Manufacturer's Website**: Follow instructions to update your GPS. 4. **Download and Install Updates**: Include map updates and software patches. 5. **Verify the Update**: Check that updates have been successfully applied. 6. **Test the Device**: Ensure it functions correctly with the new updates. Additional tips include backing up data, checking for firmware updates, ensuring the device is charged, and planning ahead to avoid last-minute rushes.

How do I use Siri on my Apple device ?
Siri is Apple's virtual assistant that can be used on iPhones, iPads, and Macs. To activate Siri, enable it in settings and either press the side button or say "Hey Siri." Once activated, you can use Siri for tasks such as making phone calls, sending messages, setting reminders, and more. You can also control HomeKit devices, translate languages, identify songs, search the web, and check weather forecasts with Siri. Customizing Siri includes changing its voice or language and teaching it from mistakes. Using Siri hands-free can make your life easier and more efficient.
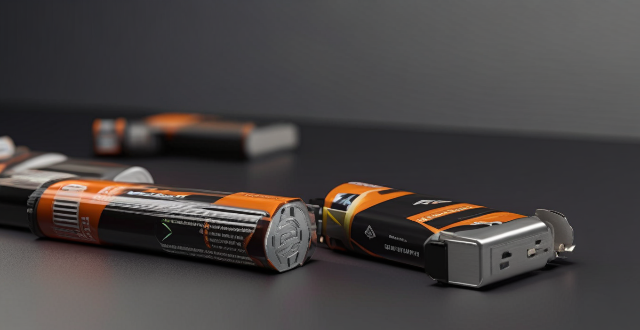
How long do zinc-carbon batteries last ?
Zinc-carbon batteries are a type of primary battery that has been widely used since the late 19th century. They are known for their reliability, low cost, and ability to provide a steady voltage output over time. However, like all batteries, zinc-carbon batteries have a finite lifespan, which depends on several factors such as battery quality, device requirements, discharge rate, and environmental conditions. To maximize their longevity, it is recommended to store them properly, use high-quality batteries, rotate batteries in devices that require multiple batteries, and avoid draining them completely.