Data Trend
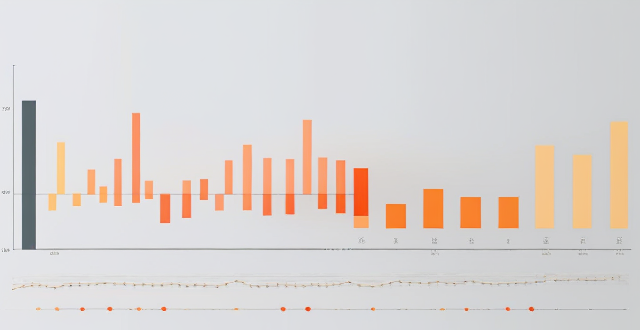
How do you interpret stock charts and graphs ?
Interpreting stock charts and graphs involves understanding various components like time frames, candlestick patterns, support/resistance levels, trend lines, technical indicators, volume, and gaps. By analyzing these elements, investors can gain insights into market trends and make informed trading decisions. However, it's essential to combine chart analysis with other forms of research and risk management strategies for optimal results.

What are the most effective methods for analyzing climate data ?
Analyzing climate data is a complex task that requires a deep understanding of the subject matter and the use of advanced statistical techniques. Some of the most effective methods for analyzing climate data include time series analysis, regression analysis, spatial analysis, principal component analysis (PCA), and machine learning algorithms. These methods help researchers to identify patterns, trends, and cycles in climate data, determine relationships between variables, analyze data with a geographical component, reduce the dimensionality of large datasets, and identify patterns and trends not apparent through traditional statistical techniques. By using these methods, researchers can gain insights into our changing planet and predict future climate conditions based on current trends.

What are the latest trends and advancements in climate data analysis technology ?
Latest Trends and Advancements in Climate Data Analysis Technology Climate data analysis has become increasingly important in recent years as scientists work to understand the impact of climate change on our planet. With advancements in technology, new methods for analyzing this data have emerged, leading to a better understanding of the complexities of the climate system. Here are some of the latest trends and advancements in climate data analysis technology: Artificial Intelligence and Machine Learning: One of the most significant developments in climate data analysis is the use of artificial intelligence (AI) and machine learning (ML). These technologies can process vast amounts of data quickly and accurately, allowing researchers to identify patterns and trends that would be difficult or impossible to detect manually. For example, AI and ML algorithms can analyze satellite images to track changes in ice coverage or monitor deforestation rates. Big Data Analytics: The volume of climate data available today is enormous, and big data analytics tools are essential for managing and interpreting this information. These tools can help researchers identify correlations between different variables, such as temperature changes and extreme weather events. They can also be used to create predictive models that forecast future climate conditions based on current trends. Cloud Computing and Remote Sensing: Cloud computing has made it possible for researchers to access and share large datasets from anywhere in the world. This has led to increased collaboration among scientists working on climate-related projects. Remote sensing technologies, such as drones and satellites, are also being used more frequently to collect climate data. These tools can provide real-time information about changes in the environment, allowing researchers to respond quickly to emerging issues. Blockchain Technology: Blockchain technology is another promising development in climate data analysis. By using a distributed ledger system, blockchain can ensure that climate data is secure, transparent, and immutable. This means that once data is recorded on the blockchain, it cannot be altered or deleted, ensuring its integrity over time. Additionally, blockchain can facilitate the sharing of climate data across organizations and countries without compromising security or privacy concerns. Citizen Science and Crowdsourcing: Citizen science and crowdsourcing initiatives have become increasingly popular ways to gather climate data. These programs involve members of the public in collecting and contributing data about their local environments. By harnessing the power of crowdsourcing, researchers can gather vast amounts of data from diverse locations around the world, providing valuable insights into global climate patterns and trends.
How do climate data analysis contribute to understanding global warming ?
Climate data analysis is essential for understanding global warming, its causes, effects, and potential solutions. Scientists collect temperature records, carbon dioxide concentrations, and sea level data to identify trends, establish correlations, and create predictive models. These efforts help develop effective strategies to mitigate the impacts of global warming.
How does climate data analysis contribute to our understanding of extreme weather events ?
Climate data analysis is essential for understanding extreme weather events. It allows scientists to identify trends, make predictions, and assess the impacts of these events on people and ecosystems. Key aspects include long-term data collection, statistical analysis, modeling techniques, vulnerability assessments, and public education. This comprehensive approach helps us prepare for and mitigate the effects of extreme weather, ultimately enhancing our resilience and adaptability in a changing climate.
What is data privacy ?
Data privacy is the protection of personal information from unauthorized use. It's important for individual rights, building trust, legal compliance, and risk mitigation. Principles include data minimization, anonymization, encryption, transparency, consent, access control, retention, integrity, and accountability. Best practices involve regular audits, employee training, updating policies, secure systems, and response plans for data breaches.

How can data analytics be used to measure teacher effectiveness and performance ?
Data analytics can be a powerful tool for measuring teacher effectiveness and performance. It allows administrators, educators, and policymakers to gain insights into various aspects of teaching and learning, leading to more informed decision-making and improvements in educational outcomes. Here's how data analytics can be leveraged to assess teacher performance: 1. Identifying Key Performance Indicators (KPIs): To begin with, it is essential to identify the key performance indicators that will be used to measure teacher effectiveness. These KPIs may include student achievement scores on standardized tests, classroom observations and evaluations, student engagement and participation levels, parent and student feedback surveys, and teacher attendance and professional development activities. 2. Collecting and Analyzing Data: Once the KPIs are established, data needs to be collected from various sources, such as student records, observation reports, and survey responses. This data should then be analyzed using statistical methods and data visualization techniques to identify patterns, trends, and correlations. 3. Interpreting Results and Making Informed Decisions: After analyzing the data, it is crucial to interpret the results and make informed decisions based on the findings. This process involves considering contextual factors, such as school resources, student demographics, and external influences, when evaluating teacher performance. 4. Continuous Monitoring and Feedback Loop: Finally, it is essential to establish a continuous monitoring system and feedback loop to ensure ongoing improvement in teacher effectiveness. This involves regularly collecting and analyzing data, providing constructive feedback to teachers, and implementing changes based on the insights gained from the data.
How does data encryption affect computer performance ?
Data encryption is crucial for securing data but can affect computer performance by increasing processor load, memory usage, disk I/O, network latency, and reducing battery life.

What are the latest trends in sports fashion ?
The article discusses the latest trends in sports fashion, including athleisure wear, sustainable sportswear, bright colors and patterns, high-tech fabrics, and accessories. It highlights how these trends focus not only on functionality and performance but also on style and individuality. The article encourages readers to incorporate these trends into their wardrobe to stay ahead of the curve and make a statement both in and out of the gym.

What are the latest trends in digital marketing ?
The article discusses the latest trends in digital marketing, including personalization, voice search optimization, video marketing, influencer marketing, chatbots and AI, and social media stories. Personalization involves using data analytics to create personalized experiences for customers, while voice search optimization requires optimizing content for voice search by using long-tail keywords and natural language. Video marketing is a popular trend that involves engaging with the audience through video content, while influencer marketing allows brands to tap into an influencer's loyal following to promote their products or services. Chatbots and AI are being used to automate customer service tasks and provide personalized recommendations to customers. Social media stories have become a popular way for brands to connect with their audience through short-form content that disappears after 24 hours. The article concludes that staying up-to-date with these trends is essential for any business looking to succeed online.
Why is data encryption important for online security ?
Data encryption is crucial for online security, protecting dataData encryption is crucial for online security, protecting data the financial impact of breaches It has evolved from ancient uses to a critical tool in today's digital landscape, with AI optimizing key management and enhancing algorithms.

What is the importance of market trends in stock analysis ?
Market trends play a crucial role in stock analysis by providing insights into the overall direction and momentum of the market. There are three types of market trends: uptrends, downtrends, and sideways trends. Understanding market trends is essential for making informed investment decisions. By analyzing market trends, investors can identify potential opportunities and risks associated with specific stocks or sectors. To effectively use market trends in stock analysis, investors should first identify the current market trend and then analyze individual stocks or sectors relative to the overall market. Make informed investment decisions based on your analysis of market trends and individual stocks or sectors. Monitor changes in market trends and adjust your investment strategy accordingly.

What are the latest fashion trends among celebrities ?
The latest fashion trends among celebrities include athleisure, oversized silhouettes, monochromatic outfits, chunky shoes, pastel colors, and sustainable fashion. These trends are all about comfort, ease, and expressing one's unique style while still being environmentally conscious.

How does global shopping influence fashion trends ?
Global shopping has significantly impacted fashion trends by increasing exposure to diverse styles, accelerating trend adoption, promoting international designers, fostering cross-cultural collaborations, supporting sustainable fashion, and affecting local markets economically.

What are the benefits of having an unlimited data plan ?
An unlimited data plan offers benefits such as no data caps or overage charges, the ability to stream videos and music without worrying about data usage, using multiple devices simultaneously, working from anywhere, enjoying online gaming and social media, and better value for money.

How do data protection regulations handle sensitive personal data ?
Handling sensitive personal data under data protection regulations requires strict adherence to principles such as consent, minimization, purpose limitation, and security. Regulations like the GDPR in the EU, CCPA in the US, and PIPEDA in Canada impose specific conditions for processing sensitive information. Organizations must adopt best practices including assessment, privacy impact assessments, employee training, access controls, and monitoring to ensure compliance and protect individuals' privacy rights.
What are the latest trends in educational technology innovation ?
The text describes the latest trends in educational technology innovation, including personalized learning, artificial intelligence (AI), augmented reality (AR) and virtual reality (VR), mobile learning, and gamification. Personalized learning tailors instruction to meet individual student needs, while AI analyzes data from student performance to provide personalized recommendations for improvement. AR and VR create immersive learning experiences through simulations and virtual field trips. Mobile learning uses mobile devices to deliver educational content and facilitate communication between students and teachers. Gamification incorporates game design elements into non-game contexts, such as education, to make learning more fun and engaging. The benefits of these trends include improved student engagement and motivation, increased retention and understanding of material, better preparation for future careers and lifelong learning, and the development of important skills such as critical thinking, problem-solving, and collaboration.
What is the difference between data privacy and data protection ?
The text discusses the difference between data privacy and data protection, emphasizing that understanding these concepts is crucial for managing personal information responsibly. Data privacy focuses on individual rights to control personal information, while data protection emphasizes organizational measures to safeguard that information. Both are essential for building trust and ensuring responsible data handling.
What role do data protection officers play under data protection laws ?
Data protection officers (DPOs) are crucial for ensuring compliance with data protection laws in organizations. They advise on compliance, develop policies, ensure adherence to regulations, educate stakeholders, and act as a point of contact for personal data requests.
Can data encryption prevent data breaches and cyber attacks ?
Data encryption is a crucial security measure that can significantly reduce the risk of data breaches and cyber attacks by converting plain text into an unreadable format. However, it does not completely eliminate the risk of data breaches and cyber attacks. Encryption works through complex algorithms to scramble data so that it appears as random characters, requiring a secret key (or password) to decrypt the data back into its original form. There are two main types of encryption: symmetric and asymmetric. While encryption offers benefits such as confidentiality, integrity, authentication, and non-repudiation, it also has limitations including key management challenges, performance overhead, compatibility issues, human error, and advanced persistent threats (APTs). Therefore, organizations should implement other security measures such as firewalls, intrusion detection systems, regular security audits, and employee training programs to minimize the risk of cyber threats.
How do unlimited data plans differ from traditional data plans ?
Data plans are essential for internet usage, with unlimited and traditional data plans being the main types. Unlimited plans offer no data limits, predictable costs, and suit heavy users, while traditional plans have data limits, variable costs, and suit light users. The key differences include data limits, cost, and usage scenarios. Choosing the right plan depends on individual needs and usage patterns.

What is data encryption and how does it work ?
Data encryption is a crucial cybersecurity measure that transforms plaintext into ciphertext, protecting it from unauthorized access. It involves the use of complex algorithms and secret decryption keys. Encryption is significant for securing data at rest, in transit, and during processing, helping meet compliance requirements and reducing financial risks associated with data breaches. Its evolution includes historical precursors and wartime innovations, with AI expected to enhance its capabilities in the future.

What happens to my data during an iPhone repair ?
When you send your iPhone for repair, the repair center will take several steps to protect your data, including diagnostics, backup, data protection, testing, verification, and return of your device.

What are the rules regarding data breaches under data protection regulations ?
Data protection regulations have been established to ensure the confidentiality, integrity, and availability of personal data. These regulations set out specific rules regarding data breaches that must be followed by organizations that handle personal data. The key rules regarding data breaches under data protection regulations include notification of data breaches, mitigating their impact, record-keeping and reporting, penalties for non-compliance, and best practices for preventing data breaches. By adhering to these rules and implementing best practices, organizations can reduce the risk of data breaches and protect individuals' personal data.

How do we analyze the data collected from environmental monitoring ?
Analyzing data from environmental monitoring involves several steps, including data cleaning, descriptive analysis, inferential statistics, time series and spatial analyses, multivariate techniques, and reporting findings. These steps help understand the current state of the environment and identify potential issues.
What are the consequences of a data breach ?
This text discusses the consequences of a data breach, including financial losses, loss of trust, reputation damage, and regulatory fines. It also highlights the long-term impact on business, legal implications, and personal impact such as identity theft and emotional distress. The text suggests mitigating measures such as implementing strong security measures, training employees, having a response plan, regularly updating systems, limiting access to sensitive data, backing up data, and insuring against data breaches.

Why is data privacy important ?
Data privacy is crucial in the digital age, protecting individuals and benefiting organizations. It ensures control over personal information, prevents misuse, and builds trust. Organizations mitigate risks, gain customer loyalty, and comply with laws by prioritizing data privacy. Key principles include transparency, individual control, data minimization, and security measures. Data privacy will continue to shape the relationship between individuals and technology, balancing innovation and privacy rights.

Can you explain the concept of 'data minimization' in data protection laws ?
Data minimization is a crucial principle in data protection laws that requires organizations to collect and process only the minimum amount of personal data necessary for specified, explicit, and legitimate purposes. This concept aims to protect individuals' privacy by limiting the potential harm that can result from the misuse or breach of their personal information. Key aspects of data minimization include collection limitation, purpose specification, data retention, data security, and accountability and transparency. Implementing robust security measures is crucial to ensure the confidentiality, integrity, and availability of personal data. Adhering to data minimization principles helps organizations comply with various data protection laws, fosters trust between individuals and organizations, reduces the risk of privacy breaches and violations, mitigates potential damage caused by cyberattacks or data breaches, and leads to cost savings for organizations due to reduced storage requirements and associated management costs.

Can blockchain technology improve data security and privacy ?
Blockchain technology has been touted as a revolutionary tool that can improve data security and privacy. Its decentralized nature, encryption, and transparency make it difficult for attackers to compromise the network. Additionally, its anonymity, control over personal data, and smart contracts enhance privacy by giving individuals more control over their information.

Do unlimited data plans really provide unrestricted internet access ?
Unlimited data plans are marketed as offering unrestricted internet access, but there are often limitations in practice. These include network management practices during peak hours, fair use policies that may reduce speeds for excessive usage, and throttling after reaching certain data thresholds. Additionally, coverage areas and hidden costs can also impact the user experience. It's important to understand the specific terms of your plan before assuming you'll have completely unfettered access.