Network Issue

Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.
Are there any tools to help diagnose network latency issues ?
Network latency issues can be frustrating and detrimental to the performance of applications and services. Fortunately, there are several tools available that can help diagnose and troubleshoot these issues. Some popular tools used for network latency diagnosis include Ping, Traceroute, MTR (My Traceroute), Netstat, Tcpdump, and Wireshark. Each tool has its own strengths and weaknesses, so it's important to choose the right one based on your specific needs and circumstances. By using these tools effectively, you can identify and resolve latency problems quickly and efficiently.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.

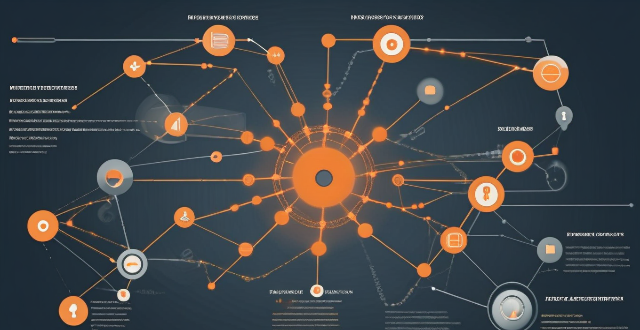
How can I detect and prevent network intrusions ?
To detect and prevent network intrusions, implementTo detect and prevent network intrusions, implement approach that includes: conducting training employees on security best practices, and regularly updating software and firmware. This comprehensive approach can significantly reduce the risk of network intrusions and protect an organization's valuable assets.
How do I troubleshoot a faulty network connection device ?
This text provides a step-by-step guide on how to troubleshoot a faulty network connection device. It starts by identifying the problem, checking physical connections, restarting the device, checking network settings, updating firmware, checking for interference, and finally contacting support if all else fails. The text emphasizes the importance of patience and perseverance in troubleshooting technical issues.
How does network congestion affect internet speed and how can it be managed ?
Network congestion slows down internet speed by causing delays, packet loss, and reduced throughput. Effective management strategies such as traffic shaping, load balancing, caching, QoS settings, infrastructure upgrades, CDNs, and congestion control algorithms can mitigate these issues and improve overall network performance.
How can I reduce network latency in my home ?
To reduce network latency in your home, check your internet speed, upgrade your router, use wired connections, optimize router settings, limit bandwidth hogs, place your router strategically, use a Wi-Fi extender or mesh network, and close unused applications and tabs.
Can climate change be considered a human rights issue ?
The text discusses the impact of climate change on human rights, focusing on health and safety, access to resources, displacement and migration, and intersectionality. It argues that climate change can be considered a human rights issue because it has the potential to violate several fundamental rights enshrined in international law. The text concludes that addressing climate change is crucial for protecting and promoting human rights globally.

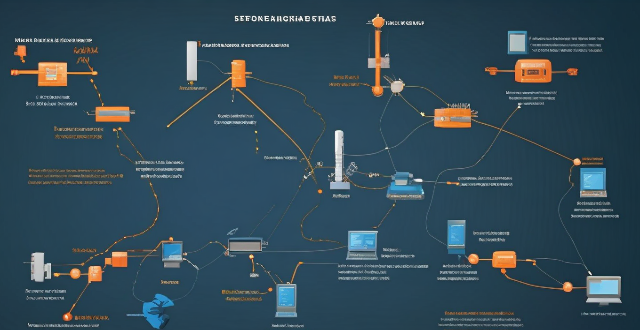
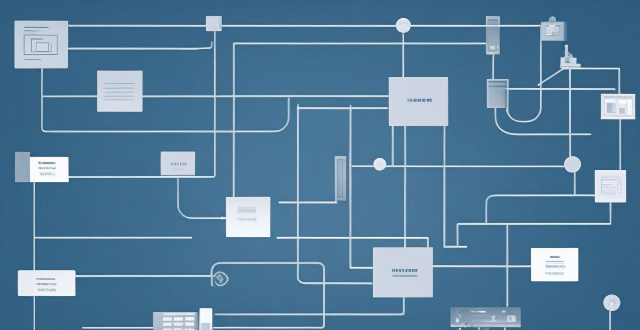
How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.
What role does caching play in network optimization ?
Caching is crucial for network optimization, improving dataCaching is crucial for network optimization, improving data speed by storing frequently accessed data improving data retrieval performance and speed by storing frequently accessed data in temporary storage areas. It reduces latency, decreases bandwidth usage, improves scalability, enhances resilience, optimizes content delivery, reduces server load, improves data consistency, and increases availability. These benefits make caching essential for improving network infrastructure performance and reliability.

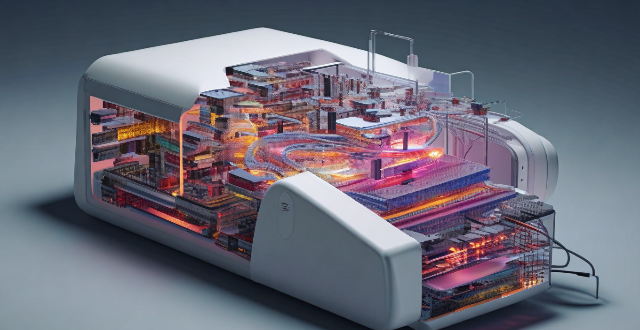
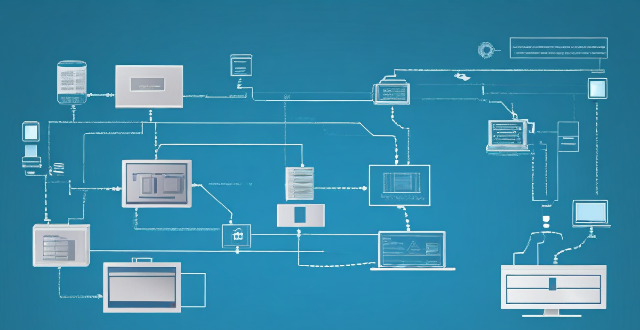
How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

Are there any known issues or bugs with the latest iOS update ?
Summary: The latest iOS update has introduced several known issues and bugs, including battery drain, Wi-Fi connectivity problems, app crashes and freezes, and other minor glitches. To resolve these issues, users can try steps such as checking app usage, adjusting settings, updating apps, restarting devices, and contacting support for further assistance.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

Why is it important to address violence against women as a human rights issue ?
Violence against women is a widespread problem that violates basic human rights and has far-reaching consequences for individuals, families, communities, and society at large. Addressing violence against women as a human rights issue is essential for upholding these basic rights, promoting gender equality, breaking the cycle of poverty and marginalization, and fulfilling our legal obligations under international law. By raising awareness about this issue and working towards creating a world where all individuals can live free from fear and violence, we can help create a more equitable and just society for all.
What technology is used to extend network coverage in remote locations ?
In remote locations, several technologies are used to extend network coverage, including satellite internet, wireless broadband (Wi-Fi), cellular data, long-range radio networks (LoRaWAN), and fiber optic cables. The choice of technology depends on factors such as cost, availability, and the specific needs of the users in those areas.
How can we address the issue of climate refugees in a just and humane way ?
The text discusses the urgent issue of climate refugees, who are individuals forced to leave their homes due to climate change impacts like rising sea levels and desertification. It outlines a comprehensive approach to address this issue in a just and humane way, including recognizing their rights under international law, providing safe shelter and basic needs, promoting economic opportunities, strengthening international cooperation, and investing in climate change mitigation and adaptation measures. The goal is to create a more equitable and resilient world for all, including climate refugees.
Can network slicing improve internet speed and reliability ?
Network slicing is a concept that divides a physical network into multiple virtual networks, each optimized for a specific use case. This approach can improve internet speed and reliability by enabling efficient resource allocation, enhancing performance through customization and optimization, and improving reliability through isolation and scalability. However, effective implementation requires careful planning and coordination among stakeholders involved in the network infrastructure.
How does network congestion impact latency ?
The impact of network congestion on latency can be significant and can have a negative effect on the overall performance of the network. This can include increased transmission time, higher drop rates, reduced bandwidth availability, and impacts on application performance. It is important for network administrators to monitor and manage network traffic to minimize the impact of congestion on latency and ensure that applications continue to function properly.
Can you explain the function of a network switch in a home network setup ?
The article discusses the function of a network switch in a home network setup. The primary function of a network switch is to connect multiple devices together, either through Ethernet cables or wireless connections. It also manages data traffic within the network by forwarding data packets to their intended destination based on their IP address. Additionally, network switches enhance network performance by providing dedicated bandwidth to each connected device and prioritizing certain types of traffic over others. Finally, network switches come with various security features that help protect your home network from unauthorized access and cyber threats.

How do firewalls contribute to network security ?
Firewalls are crucial for network security, offeringFirewalls are crucial for network security, offering, blocking unwanted connections, preventing preventing network intrusion, enforcing security policies, providing VPN support, integrating with other security systems, protecting against known threats, offering customizable features, ensuring scalability and performance, and reducing the risk of data breach.

How can I improve my home's Wi-Fi network coverage ?
The text provides tips on how to improve Wi-Fi network coverage at home, including upgrading the router, changing its location, using extenders or mesh networks, updating firmware, adjusting settings, limiting bandwidth-heavy activities, replacing old devices, and using wired connections where possible.

Why do some areas have poor network coverage ?
Poor network coverage is a multifaceted issue influenced by geography, economics, technology, regulation, and environmental factors. Addressing these challenges requires a collaborative effort from governments, private sectors, and communities to ensure that connectivity is accessible to all, regardless of their location.

How does a network bridge improve internet connectivity ?
A network bridge is a device that connects two or more networks at the data link layer, offering benefits such as reduced congestion, increased security, enhanced performance, cost-effectiveness, and compatibility. It improves internet connectivity by segregating traffic, filtering based on MAC addresses, optimizing routing, and extending the use of existing infrastructure. Bridges are applicable in home, enterprise, and public access networks for connecting devices, separating departmental networks, and providing guest access.
What industries will benefit the most from network slicing capabilities ?
The article discusses the concept of network slicing, a technology derived from software-defined networking (SDN) and network function virtualization (NFV), which allows the partitioning of physical networks into multiple virtual networks to optimize resource allocation according to specific service requirements. It outlines the key benefits and applications of network slicing in various sectors such as automotive, healthcare, manufacturing, energy, financial services, and entertainment and media. The conclusion highlights the potential of network slicing to revolutionize communication systems and enhance service delivery, operational efficiency, and user experience across different industries.
What is the role of firewalls in network security protection ?
Firewalls are crucial for network security protection, acting as a barrier between trusted and untrusted networks to prevent unauthorized access and block malicious traffic. They monitor network activity for potential threats, with various types including packet-filtering, stateful inspection, application-level, and next-generation firewalls. Firewalls offer benefits such as access control, threat prevention, visibility and auditing, and compliance enforcement. Best practices for deploying firewalls include implementing a multi-layered defense strategy, regularly updating firewall rules and policies, monitoring logs and alerts, conducting regular penetration testing, and training staff on firewall management and maintenance.

How can I ensure the security of my wireless network ?
Securing a wireless network involves changing the default administrator password, using WPA2 encryption, enabling network encryption, using a firewall, and updating firmware regularly.