Data User

How do data protection regulations impact the use of cookies on websites ?
Data protection regulations have significant impacts on the use of cookies on websites. Website owners must comply with strict rules regarding explicit consent from users, transparency and disclosure of cookie use, minimization of data collection, data security, and avoidance of penalties for non-compliance. By doing so, they can protect user privacy and build trust while still providing an optimal user experience through the use of cookies.

How do data protection regulations apply to social media platforms ?
This article discusses the crucial role of data protection regulations in safeguarding user information on social media platforms. It outlines key principles such as transparency, purpose limitation, and accountability that guide the handling of personal data by these platforms. The responsibilities of both social media platforms and users are highlighted, emphasizing the importance of informed consent, security measures, and user control. The article concludes by stressing the mutual responsibility of platforms and users in promoting a safe online environment through adherence to data protection regulations.

What is network latency and how does it impact user experience ?
Network latency is the delay in data transmission over a network, influenced by factors such as distance, congestion, and hardware limitations. It negatively impacts user experience in online gaming, video conferencing, streaming services, web browsing, and online shopping, leading to frustration and reduced engagement. Reducing latency through optimized network infrastructure can enhance user satisfaction.

**Is my data safe with iCloud's privacy features ?
iCloud, Apple's cloud storage service, offers several privacy and security features to protect user data. These include Private Relay for anonymous browsing, end-to-end encryption for secure transmission, two-factor authentication for account security, tracking prevention for apps and websites, data breach notifications, encrypted cloud storage, privacy reports, password security monitoring, child safety features, and regular security updates. While these features provide robust protection, users should still practice good digital hygiene to further safeguard their data.

Can I use multiple user accounts on my Apple computer ?
Using multiple user accounts on an Apple computer allows for privacy, security, customization, and parental controls. To set up additional user accounts, open System Preferences, click on Users & Groups, unlock the preferences pane, add a new user account, customize it, and repeat for each additional user. Switching between accounts can be done through the Apple menu by selecting "Log Out" or "Switch User."

How do remote education platforms ensure data privacy and security ?
Remote education platforms ensure data privacy and security through encryption, access controls, two-factor authentication, regular security audits, and data retention policies. These measures help protect user data during transmission and storage, restrict access to sensitive information, add an extra layer of security, identify and fix vulnerabilities, and minimize the risk of data breaches.
What are some common ways that companies collect and use personal data ?
Companies employ various direct and indirect methods to collect personal data, which they then use for marketing, product development, enhancing customer experiences, and ensuring security.
What role do technology companies play in protecting privacy rights ?
The role of technology companies in protecting privacy rights is crucial. They are responsible for ensuring that user data is collected, stored, and used responsibly. This includes providing transparency about data collection practices, obtaining explicit consent, limiting data collection to necessary information, and implementing robust security measures. Technology companies should also allow users to control their personal information by providing easy access, modification, and deletion tools, as well as options to opt-out of data sharing. By following these best practices, technology companies can build trust with users and promote a culture of privacy protection within the industry.

Why is data privacy important ?
Data privacy is crucial in the digital age, protecting individuals and benefiting organizations. It ensures control over personal information, prevents misuse, and builds trust. Organizations mitigate risks, gain customer loyalty, and comply with laws by prioritizing data privacy. Key principles include transparency, individual control, data minimization, and security measures. Data privacy will continue to shape the relationship between individuals and technology, balancing innovation and privacy rights.

Do unlimited data plans really provide unrestricted internet access ?
Unlimited data plans are marketed as offering unrestricted internet access, but there are often limitations in practice. These include network management practices during peak hours, fair use policies that may reduce speeds for excessive usage, and throttling after reaching certain data thresholds. Additionally, coverage areas and hidden costs can also impact the user experience. It's important to understand the specific terms of your plan before assuming you'll have completely unfettered access.

Will my unlimited data plan slow down after reaching a certain amount of data usage ?
Throttling refers to the intentional slowing down of internet speeds by an internet service provider (ISP) once a user reaches a certain threshold of data usage within a billing cycle. While unlimited data plans do not have a specific data cap like limited data plans, some ISPs may still throttle your speeds under certain circumstances such as network congestion, fair use policy, time of day, and data prioritization. It is essential to read the terms and conditions of your unlimited data plan carefully to understand any restrictions and be aware of the factors that can influence whether your plan will be throttled.

**What exactly is end-to-end encryption offered by iCloud ?
End-to-end encryption is a security measure that ensures data transmitted between two endpoints, such as a user's device and iCloud, can only be read by the intended recipient. This means that even if someone intercepts the data during transmission, they will not be able to access or modify it without the proper encryption keys. Key features of end-to-end encryption offered by iCloud include: 1. Data Privacy: End-to-end encryption ensures that your data remains private and secure while being transmitted over the internet. 2. Security: With end-to-end encryption, even Apple cannot access your data because they do not hold the encryption keys. Only you and the recipient of your data have access to the keys needed to decrypt the information. 3. Trustworthiness: By offering end-to-end encryption, iCloud demonstrates its commitment to protecting users' privacy and building trust with its customers. 4. Compliance with Regulations: End-to-end encryption also helps iCloud comply with various regulations related to data protection and privacy, such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States. 5. User Control: End-to-end encryption gives users more control over their data by allowing them to choose when and how their information is shared. For example, users can decide whether to use end-to-end encryption for specific types of data or for all their data stored in iCloud. Overall, end-to-end encryption offered by iCloud provides several benefits, including enhanced data privacy, security, trustworthiness, compliance with regulations, and user control.

How do companies collect and use my personal data online ?
Companies collect and use personal data online for various purposes, including marketing, advertising, customer service, and improving their products or services. They do this through cookies and tracking technologies, social media platforms, email marketing, and customer service interactions. By analyzing this data, companies can gain insights into user behavior and preferences, which they can use to improve their products or services and target users with personalized advertising.

Can you explain the concept of 'data minimization' in data protection laws ?
Data minimization is a crucial principle in data protection laws that requires organizations to collect and process only the minimum amount of personal data necessary for specified, explicit, and legitimate purposes. This concept aims to protect individuals' privacy by limiting the potential harm that can result from the misuse or breach of their personal information. Key aspects of data minimization include collection limitation, purpose specification, data retention, data security, and accountability and transparency. Implementing robust security measures is crucial to ensure the confidentiality, integrity, and availability of personal data. Adhering to data minimization principles helps organizations comply with various data protection laws, fosters trust between individuals and organizations, reduces the risk of privacy breaches and violations, mitigates potential damage caused by cyberattacks or data breaches, and leads to cost savings for organizations due to reduced storage requirements and associated management costs.
How has climate data analysis evolved over the past decade ?
Over the past decade, climate data analysis has seen significant advancements in various aspects, including improved data collection through advanced satellite technology and ground-based measurements, advanced modeling techniques such as complex climate models and data assimilation, enhanced computational power with supercomputers and cloud computing, big data analytics involving machine learning and AI, open data initiatives promoting public availability of data and collaborative platforms, and an interdisciplinary approach integrating multiple fields and engaging the public. These developments have revolutionized our understanding of the Earth's climate system and paved the way for more accurate and comprehensive climate research and policy-oriented decision support tools.

How do you use data analytics to improve your digital marketing efforts ?
In the digital age, data analytics has become an indispensable tool for improving marketing strategies. By analyzing consumer behavior and preferences, businesses can tailor their marketing efforts to better suit their target audience, ultimately leading to increased engagement and conversion rates. To improve your digital marketing efforts using data analytics, follow these steps: 1. Identify Key Performance Indicators (KPIs) based on your marketing objectives such as increasing website traffic or boosting sales. 2. Collect and analyze data using tools like Google Analytics and social media analytics platforms to identify trends and areas for improvement. 3. Optimize your marketing strategy by adjusting content, creating targeted campaigns, and refining ad spend based on performance. 4. Continuously test and refine your approach through A/B testing and iterating based on results to optimize performance. By integrating data analytics into your digital marketing efforts, you gain valuable insights that allow you to make informed decisions and optimizations. This systematic approach not only enhances the effectiveness of your marketing campaigns but also helps you stay ahead in a competitive market. Remember, the key is to continuously monitor, analyze, and adapt based on the data you collect.
What is data privacy ?
Data privacy is the protection of personal information from unauthorized use. It's important for individual rights, building trust, legal compliance, and risk mitigation. Principles include data minimization, anonymization, encryption, transparency, consent, access control, retention, integrity, and accountability. Best practices involve regular audits, employee training, updating policies, secure systems, and response plans for data breaches.

Can smart home gadgets learn user preferences and adapt accordingly ?
Smart home gadgets can learn user preferences and adapt accordingly through machine learning algorithms. Examples include personalized lighting, energy efficiency, security, entertainment, and voice assistants. These devices make our lives more convenient, comfortable, and efficient.

Are there any restrictions on what kinds of apps can be sold on the App Store ?
The App Store imposes restrictions on application content, developer behavior, sales and distribution, user experience, and more to maintain a high standard of quality and security for users. Developers must adhere to these guidelines to successfully sell their applications on the platform.
Can you explain some lesser-known tips and tricks for customizing the user interface and experience using hidden features in iOS ?
This article provides a summary of some lesser-known tips and tricks for customizing the user interface and experience using hidden features in iOS. It covers topics such as Accessibility Shortcut, Reduce Motion, Increase Contrast, Reduce Transparency, Customize Control Center, Use Siri with Third-Party Apps, Use Split View in Safari, and Use Keyboard Shortcuts. These hidden features can help users personalize their device and make it more accessible and efficient to use.

How do wearable devices integrate with health management apps to provide more accurate data on physical activity levels ?
Wearable devices and health management apps work together to provide accurate physical activity data. The integration process involves data collection, transmission, analysis, visualization, and feedback. This collaboration offers benefits such as accurate data tracking, personalized insights, goal setting and tracking, and improved health outcomes. Examples of integrated systems include Fitbit and Fitbit App, Apple Watch and Apple Health App, and Garmin Devices and Garmin Connect App.

Are there any limitations on video streaming quality with unlimited data plans ?
Unlimited data plans offer convenience but may have limitations on video streaming quality due to factors like data throttling, network congestion, platform restrictions, and device capabilities. To optimize your experience, choose a reliable network provider, optimize your device settings, use high-quality platforms, and avoid peak usage hours.
How does data encryption affect computer performance ?
Data encryption is crucial for securing data but can affect computer performance by increasing processor load, memory usage, disk I/O, network latency, and reducing battery life.
Why is data encryption important for online security ?
Data encryption is crucial for online security, protecting dataData encryption is crucial for online security, protecting data the financial impact of breaches It has evolved from ancient uses to a critical tool in today's digital landscape, with AI optimizing key management and enhancing algorithms.

How does two-factor authentication enhance security ?
Two-factor authentication (2FA) is a security process that requires two different factors to verify the user's identity, enhancing security by reducing the risk of unauthorized access, providing alerts for suspicious activities, protecting against various types of attacks, increasing user confidence in online services, and helping maintain compliance with security standards. Its implementation should be carefully planned considering both security requirements and user convenience.
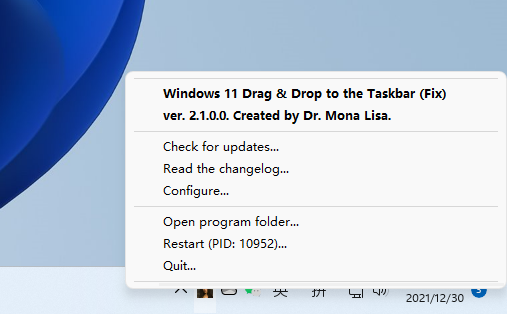
Win11 user ecstasy: the third-party gadget can realize the function of dragging and dropping to open files on the taskbar (with download)

What are the benefits of having an unlimited data plan ?
An unlimited data plan offers benefits such as no data caps or overage charges, the ability to stream videos and music without worrying about data usage, using multiple devices simultaneously, working from anywhere, enjoying online gaming and social media, and better value for money.