Risk Data

How can climate data analysis help in disaster risk reduction and management ?
Climate data analysis is crucial for disaster risk reduction and management. It helps identify high-risk areas, predict future weather patterns, develop mitigation strategies, and enhance disaster response and recovery efforts. By analyzing past and current climate data, we can better prepare for and respond to natural disasters such as floods, hurricanes, wildfires, and droughts.
What role do scientists play in climate risk assessments ?
Scientists are crucial in climate risk assessments, analyzing data, developing models, and providing recommendations for mitigating risks. They collect data from multiple sources and use statistical methods to identify trends, create computer models to predict impacts, develop strategies to mitigate risks, and communicate their findings to build support for policies and actions.
What is data privacy ?
Data privacy is the protection of personal information from unauthorized use. It's important for individual rights, building trust, legal compliance, and risk mitigation. Principles include data minimization, anonymization, encryption, transparency, consent, access control, retention, integrity, and accountability. Best practices involve regular audits, employee training, updating policies, secure systems, and response plans for data breaches.

Can I upgrade the storage capacity of my iPhone without losing any data ?
Upgrading the storage capacity of an iPhone without losing any data is possible but risky. Options include official Apple upgrades, third-party repair services, and using cloud storage. Risks include data loss, voided warranty and insurance, compatibility issues, and high costs. It is recommended to carefully consider the potential risks before attempting a storage upgrade.
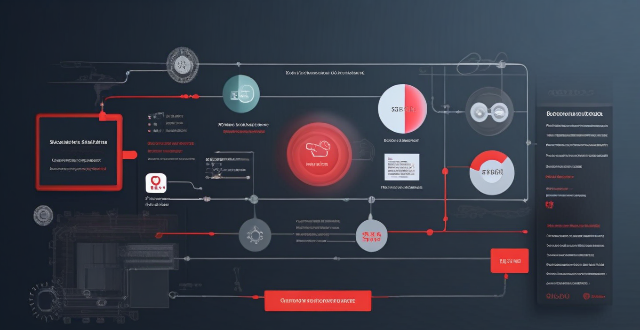
Can data encryption prevent data breaches and cyber attacks ?
Data encryption is a crucial security measure that can significantly reduce the risk of data breaches and cyber attacks by converting plain text into an unreadable format. However, it does not completely eliminate the risk of data breaches and cyber attacks. Encryption works through complex algorithms to scramble data so that it appears as random characters, requiring a secret key (or password) to decrypt the data back into its original form. There are two main types of encryption: symmetric and asymmetric. While encryption offers benefits such as confidentiality, integrity, authentication, and non-repudiation, it also has limitations including key management challenges, performance overhead, compatibility issues, human error, and advanced persistent threats (APTs). Therefore, organizations should implement other security measures such as firewalls, intrusion detection systems, regular security audits, and employee training programs to minimize the risk of cyber threats.
Why is data encryption important for online security ?
Data encryption is crucial for online security, protecting dataData encryption is crucial for online security, protecting data the financial impact of breaches It has evolved from ancient uses to a critical tool in today's digital landscape, with AI optimizing key management and enhancing algorithms.

What are the rules regarding data breaches under data protection regulations ?
Data protection regulations have been established to ensure the confidentiality, integrity, and availability of personal data. These regulations set out specific rules regarding data breaches that must be followed by organizations that handle personal data. The key rules regarding data breaches under data protection regulations include notification of data breaches, mitigating their impact, record-keeping and reporting, penalties for non-compliance, and best practices for preventing data breaches. By adhering to these rules and implementing best practices, organizations can reduce the risk of data breaches and protect individuals' personal data.

Can you explain the concept of 'data minimization' in data protection laws ?
Data minimization is a crucial principle in data protection laws that requires organizations to collect and process only the minimum amount of personal data necessary for specified, explicit, and legitimate purposes. This concept aims to protect individuals' privacy by limiting the potential harm that can result from the misuse or breach of their personal information. Key aspects of data minimization include collection limitation, purpose specification, data retention, data security, and accountability and transparency. Implementing robust security measures is crucial to ensure the confidentiality, integrity, and availability of personal data. Adhering to data minimization principles helps organizations comply with various data protection laws, fosters trust between individuals and organizations, reduces the risk of privacy breaches and violations, mitigates potential damage caused by cyberattacks or data breaches, and leads to cost savings for organizations due to reduced storage requirements and associated management costs.
What is the difference between data privacy and data protection ?
The text discusses the difference between data privacy and data protection, emphasizing that understanding these concepts is crucial for managing personal information responsibly. Data privacy focuses on individual rights to control personal information, while data protection emphasizes organizational measures to safeguard that information. Both are essential for building trust and ensuring responsible data handling.
What is the role of encryption in securing data transmission ?
Encryption is crucial for securing data transmission by converting plain text into unreadable ciphertext, ensuring confidentiality, integrity, and authentication. It protects sensitive information, prevents data tampering, enhances trust, complies with regulations, and reduces the risk of data breaches. Two main types of encryption are symmetric and asymmetric encryption, each using different keys for encryption and decryption.

How do remote education platforms ensure data privacy and security ?
Remote education platforms ensure data privacy and security through encryption, access controls, two-factor authentication, regular security audits, and data retention policies. These measures help protect user data during transmission and storage, restrict access to sensitive information, add an extra layer of security, identify and fix vulnerabilities, and minimize the risk of data breaches.
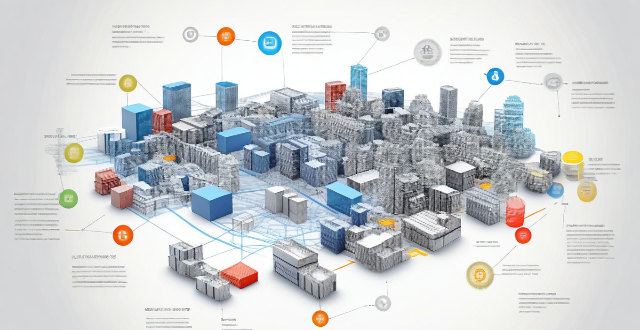
What role do technology and data analytics play in improving disaster risk management strategies ?
This article explores how technology and data analytics can be used to improve disaster risk management strategies. It discusses the identification of potential hazards, assessment of vulnerabilities and capacities, monitoring and early warning systems, response coordination and information sharing, and recovery planning and implementation. The article emphasizes that technology and data analytics play a crucial role in enhancing preparedness, response, and recovery efforts, and predicting future disaster events based on historical data.

Why is data privacy important ?
Data privacy is crucial in the digital age, protecting individuals and benefiting organizations. It ensures control over personal information, prevents misuse, and builds trust. Organizations mitigate risks, gain customer loyalty, and comply with laws by prioritizing data privacy. Key principles include transparency, individual control, data minimization, and security measures. Data privacy will continue to shape the relationship between individuals and technology, balancing innovation and privacy rights.

How can companies prevent data breaches ?
Data breaches can be devastating for companies, leadingData breaches can be devastating for companies, leadingal damage, and legal consequences To prevent data breaches, companies should implement a multi-layered approach that includes the following strategies: 1\. Develop a Security Policy 2\. Use Encryption 3\. Implement Access Controls 4\. Educate Employees 5\. Keep Software Up-to-Date 6\. Conduct Regular Audits and Tests 7\. Have an Incident Response Plan

Can blockchain technology improve data security and privacy ?
Blockchain technology has been touted as a revolutionary tool that can improve data security and privacy. Its decentralized nature, encryption, and transparency make it difficult for attackers to compromise the network. Additionally, its anonymity, control over personal data, and smart contracts enhance privacy by giving individuals more control over their information.

What is climate risk assessment ?
Climate risk assessment is a systematic process that identifies, evaluates, and prioritizes the potential impacts of climate change on a specific region or sector. It involves analyzing the likelihood and severity of various climate-related risks, such as extreme weather events, sea level rise, and changes in temperature and precipitation patterns. The goal of climate risk assessment is to inform decision-makers about the risks associated with climate change and help them develop strategies to manage and adapt to these risks. Key components of climate risk assessment include identifying potential risks, evaluating their potential impacts, prioritizing them based on severity and likelihood of occurrence, and developing adaptation strategies to reduce potential impacts. By implementing these strategies, decision-makers can help ensure that their communities are better prepared for the challenges posed by climate change.

How can climate services help in disaster risk reduction ?
Climate services play a crucial role in disaster risk reduction by providing essential information and tools that help communities, governments, and businesses to anticipate and respond to the impacts of climate change. These services encompass a range of activities, including weather forecasting, climate monitoring, and the development of early warning systems. Climate services contribute to disaster risk reduction through several strategies, including risk assessment, preparedness planning, early warning and response, and recovery and resilience building. By leveraging these services, societies can build resilience against the increasing challenges posed by a changing climate.

What are some examples of data breaches and how do they affect individuals ?
Data breaches have become a pervasive issue in the digital age, affecting millions of individuals worldwide. These incidents can compromise sensitive information and have far-reaching consequences for those affected. In this discussion, we will explore some notable examples of data breaches and examine how they impact individuals.

What are the benefits of using data encryption in business ?
Data encryption in business offers protection of sensitive information, compliance with legal requirements, enhanced customer trust, defense against cyber threats, and controlled data access. It ensures confidentiality and integrity of communications, helps meet regulatory standards, safeguards personal data, builds customer confidence, mitigates risks of data breaches, guards against malware and ransomware, provides role-based access control, and simplifies key management. This makes encryption an essential tool for securing digital assets and strengthening a company's market position.

What is disaster risk management ?
Disaster risk management (DRM) is a comprehensive approach aimed at reducing the impact of natural and human-made disasters on communities. It involves understanding, assessing, and reducing risks through prevention, preparedness, response, and recovery strategies. The goal is to ensure that people's lives and livelihoods are not compromised by disaster events. Key components include risk assessment, hazard mitigation, early warning systems, emergency planning, community education, immediate action, coordination, rehabilitation, reconstruction, and sustainable development. Best practices involve multi-stakeholder collaboration, gender sensitivity, use of technology, inclusive planning, and regular review and updating. Challenges include limited resources, political will, information gaps, and cultural differences. Effective DRM requires a multifaceted approach that considers social, economic, and environmental factors.

What is the General Data Protection Regulation (GDPR) ?
The General Data Protection Regulation (GDPR) is a comprehensive data privacy law that governs how personal information is collected, processed, and stored by organizations within the European Union (EU). It was designed to protect the rights of individuals and ensure their personal data is handled securely and transparently. Key features of GDPR include data minimization, consent, transparency, data portability, right to erasure, data protection officers (DPOs), and penalties for non-compliance. Benefits of GDPR compliance include enhanced trust between organizations and customers, risk mitigation through strong data protection measures, competitive advantage in the EU market, and increasing global relevance as other countries adopt similar laws. Challenges of GDPR compliance include complexity, cost, cultural differences leading to confusion and potential non-compliance, and technological limitations. In conclusion, the General Data Protection Regulation (GDPR) is a crucial piece of legislation that aims to protect the privacy rights of individuals within the European Union. While it presents both benefits and challenges for organizations, compliance with GDPR has become an essential aspect of modern business operations in today's digital age.

How does data analysis contribute to injury prevention in sports ?
Data analysis is a powerful tool for preventing injuries in sports. By identifying risk factors, developing prevention strategies, implementing surveillance systems, evaluating intervention effectiveness, and educating athletes and coaches, data-driven approaches can significantly reduce the likelihood of injuries. This not only protects athletes' health but also improves their performance.

How do banks manage credit risk ?
Banks manage credit risk through a variety of methods and strategies to ensure the stability of their operations and protect against potential losses. They identify and assess credit risk using credit scoring models, financial analysis, and credit reports. They mitigate credit risk through diversification, collateral and guarantees, and credit derivatives. Banks monitor and control credit risk by ongoing monitoring, loan loss reserves, and regulatory compliance. In case of credit risk events, banks recover through workout agreements, legal recourse, and communication with stakeholders. By employing these strategies, banks aim to minimize credit risk while still providing essential lending services to support economic growth and individual prosperity.
How does data encryption affect computer performance ?
Data encryption is crucial for securing data but can affect computer performance by increasing processor load, memory usage, disk I/O, network latency, and reducing battery life.

How does risk management relate to compliance and regulatory requirements ?
Risk management and compliance are interconnected aspects of organizational operations, aimed at safeguarding against potential losses and legal issues. Risk management identifies and prioritizes risks impacting objectives, while compliance ensures adherence to laws and regulations. An integrated approach enhances efficiency, and collaboration between departments is key for success. Regulatory requirements significantly influence risk management and compliance strategies, with direct rules and indirect environmental changes. Understanding these dynamics is vital for maintaining reputation and avoiding compliance breaches.

Is data encryption necessary for all types of businesses and industries ?
The Importance of Data Encryption in Modern Business Operations Data encryption is a crucial aspect of modern business operations, ensuring confidentiality, integrity, and availability of sensitive information. Different types of businesses and industries handle varying degrees of sensitive data, requiring robust security measures. Healthcare, finance, e-commerce, and legal sectors are examples where encryption is necessary due to the nature of the data they handle or regulatory requirements. However, the necessity of implementing encryption can depend on factors such as the type and amount of sensitive data, risk assessment, and compliance with legal requirements. To implement data encryption, businesses must assess their needs, develop a data protection policy, choose appropriate technologies, integrate them into systems and processes, and regularly monitor and maintain these measures. While not always necessary for every business, data encryption is often a wise investment that can protect sensitive information and ensure business continuity.

How do insurance mechanisms support disaster risk management and recovery processes ?
Insurance mechanisms play a vital role in supporting disaster risk management and recovery processes, providing financial protection to individuals, businesses, and governments against the economic impacts of natural disasters. They encourage risk mitigation measures, offer financial protection through various policies, facilitate recovery and reconstruction, invest in catastrophe modeling and research, and create public-private partnerships to improve disaster preparedness and response.

What are the risks associated with using Fintech services ?
Fintech services have revolutionized the way we manage our money, but they also come with risks. These include security risks such as phishing attacks, malware, and data breaches; privacy risks like data collection and third-party access; and financial risks including fraudulent transactions and market volatility. It is important to be aware of these risks and take steps to protect yourself when using fintech services.

How can climate data analysis inform sustainable development goals and practices ?
**Summary:** Climate data analysis is crucial for understanding environmental systems and shaping sustainable development goals (SDGs) and practices. It helps identify trends, inform policy decisions, assess environmental impacts, and guide sustainable agriculture, urban planning, and disaster risk reduction. By integrating climate data into development frameworks, we can ensure that current actions do not compromise future generations' ability to meet their needs and aspirations.
How can climate risk management help reduce the impact of climate change on the environment ?
Climate risk management is a multi-step approach that helps mitigate the effects of climate change on the environment. It involves identifying and assessing risks, prioritizing them, developing adaptation strategies, implementing mitigation efforts, fostering collaboration, and continuously monitoring outcomes. This proactive method aims to protect natural systems from adverse climate impacts, promote sustainable practices, and reduce greenhouse gas emissions. By adopting these measures, we can build resilience against climate-related risks and contribute to a more sustainable future for all.