Network Management

How does network slicing differ from traditional network management techniques ?
Network slicing, enabled by SDN and NFV, allows creating multiple virtual networks on a common infrastructure for tailored services like IoT and automotive systems. It offers dynamic resource allocation, scalability, better security, and can simplify management through automation. In contrast, traditional network management is monolithic with static resources, complex and potentially less secure. Network slicing is a more adaptable solution for diverse and growing connectivity needs.

What is the role of bandwidth management in network optimization ?
Bandwidth management is a critical component of network optimization, as it involves controlling and managing the amount of data that can be transmitted over a network at any given time. By effectively managing bandwidth, network administrators can ensure optimal performance and prevent congestion, leading to faster speeds and improved overall network efficiency. Key benefits of bandwidth management include improved network performance, reduced congestion, enhanced user experience, cost savings, and increased security. Techniques for effective bandwidth management include Quality of Service (QoS), traffic shaping, caching, compression, and load balancing. Best practices for bandwidth management involve monitoring network usage, implementing policies and guidelines, using QoS settings appropriately, updating hardware and software regularly, and educating users about proper network usage.

How does network slicing work in 5G technology ?
Network slicing is a feature of 5G technology that allows operators to create multiple virtual networks on a shared physical infrastructure. This enables them to offer customized services with specific quality of service (QoS) and quality of experience (QoE) requirements for different types of customers and applications. The implementation of network slicing involves several key components such as Network Function Virtualization (NFV), Software-Defined Networking (SDN), Network Management and Orchestration (MANO), and Policy Management. The steps involved in implementing network slicing include requirement analysis, resource allocation, virtual network function deployment, resource management, policy enforcement, monitoring and optimization, and lifecycle management. Network slicing offers benefits such as customization, resource efficiency, scalability, improved performance, and enhanced security.

What are the challenges faced during a network expansion project ?
When expanding a network, organizations may face various challenges that can impact the success of the project. These challenges include budget constraints, technical difficulties, security concerns, downtime and disruptions, training and support requirements, integration with existing systems, regulatory compliance, project management issues, change management, and future-proofing considerations. By proactively addressing these challenges, organizations can successfully complete network expansion projects while minimizing disruptions and maximizing the benefits of the expanded network.

How does network expansion affect the overall network performance ?
Network expansion can significantly impact overall performance, offering benefits such as increased bandwidth, improved redundancy, and enhanced connectivity. However, challenges like compatibility issues, security concerns, and complexity management must be addressed to maintain optimal performance. Careful planning is crucial for successful network expansion.

What is the cost involved in expanding a network ?
Expanding a network involves costs in hardware, software, labor and other areas.

What causes network latency ?
Network latency is a critical metric in networking, referring to the delay that data experiences when traveling between two points in a network. Understanding the causes of network latency is essential for optimizing productivity, collaboration, and user experience in today's digitally reliant world. The article delves into the various factors contributing to network latency and why it matters.
How does network congestion affect internet speed and how can it be managed ?
Network congestion slows down internet speed by causing delays, packet loss, and reduced throughput. Effective management strategies such as traffic shaping, load balancing, caching, QoS settings, infrastructure upgrades, CDNs, and congestion control algorithms can mitigate these issues and improve overall network performance.
What is the role of a network hub in a computer network ?
In this text, the role of a network hub in a computer network is discussed. The main functions of a network hub are data transmission, connectivity, and collision domain management. However, the device also has limitations such as bandwidth sharing, security risks, and scalability issues. Despite its importance in connecting devices and allowing resource sharing, more advanced networking devices are often used in larger and more complex networks to overcome these limitations.

What is the purpose of a VPN (Virtual Private Network) device in a business network ?
The purpose of a VPN device in a business network is to provide secure and encrypted connections for remote access to the organization's resources, ensuring that employees, partners, and customers can access the company's data and applications securely from any location. Key features include encryption, authentication, firewall protection, scalability, and flexibility. Benefits of using a VPN device in a business network include enhanced security, improved productivity, cost savings, and simplified IT management.
Are there any potential drawbacks or challenges with implementing network slicing ?
Network slicing is a promising technology that allows multiple virtual networks to coexist on a shared physical infrastructure. It enables operators to provide tailored network services for different use cases, such as enhanced mobile broadband (eMBB), ultra-reliable low-latency communications (URLLC), and massive machine-type communications (mMTC). However, there are potential drawbacks and challenges associated with implementing network slicing, including the complexity of management and orchestration, significant infrastructure investment required, standardization and interoperability issues, skill gap within organizations, and regulatory and legal aspects to consider.

How do firewalls contribute to network security ?
Firewalls are crucial for network security, offeringFirewalls are crucial for network security, offering, blocking unwanted connections, preventing preventing network intrusion, enforcing security policies, providing VPN support, integrating with other security systems, protecting against known threats, offering customizable features, ensuring scalability and performance, and reducing the risk of data breach.
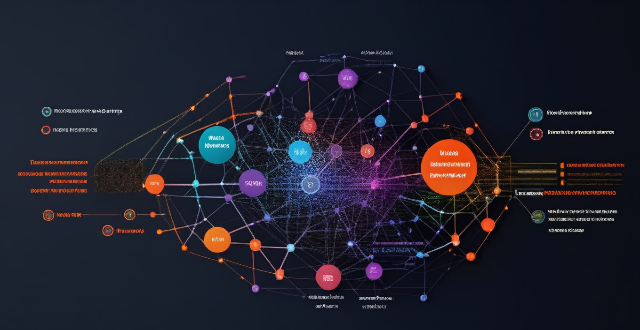
What industries will benefit the most from network slicing capabilities ?
The article discusses the concept of network slicing, a technology derived from software-defined networking (SDN) and network function virtualization (NFV), which allows the partitioning of physical networks into multiple virtual networks to optimize resource allocation according to specific service requirements. It outlines the key benefits and applications of network slicing in various sectors such as automotive, healthcare, manufacturing, energy, financial services, and entertainment and media. The conclusion highlights the potential of network slicing to revolutionize communication systems and enhance service delivery, operational efficiency, and user experience across different industries.
Can network slicing improve internet speed and reliability ?
Network slicing is a concept that divides a physical network into multiple virtual networks, each optimized for a specific use case. This approach can improve internet speed and reliability by enabling efficient resource allocation, enhancing performance through customization and optimization, and improving reliability through isolation and scalability. However, effective implementation requires careful planning and coordination among stakeholders involved in the network infrastructure.
What is the role of firewalls in network security protection ?
Firewalls are crucial for network security protection, acting as a barrier between trusted and untrusted networks to prevent unauthorized access and block malicious traffic. They monitor network activity for potential threats, with various types including packet-filtering, stateful inspection, application-level, and next-generation firewalls. Firewalls offer benefits such as access control, threat prevention, visibility and auditing, and compliance enforcement. Best practices for deploying firewalls include implementing a multi-layered defense strategy, regularly updating firewall rules and policies, monitoring logs and alerts, conducting regular penetration testing, and training staff on firewall management and maintenance.
How do communication protocols manage errors and congestion in a network ?
Communication protocols play a crucial role in managing errors and congestion in a network. They use various techniques such as checksums, acknowledgments, timers, traffic shaping, congestion control, and error recovery mechanisms to ensure reliable and efficient data transmission between devices on a network.
What are the latest techniques in network optimization ?
The article discusses the latest techniques in network optimization, which include software-defined networking (SDN), network function virtualization (NFV), machine learning and artificial intelligence (AI), edge computing, and multipath transmission control protocol (MPTCP). SDN separates the control plane from the data plane, allowing for centralized management and control of network devices. NFV replaces traditional hardware-based network functions with virtualized versions running on standard servers. Machine learning and AI enable networks to automatically detect and respond to changes in traffic patterns, optimizing performance without manual intervention. Edge computing brings computational resources closer to the end users or devices, reducing latency and improving overall network performance. MPTCP allows multiple paths between two endpoints to be used simultaneously, reducing congestion and improving reliability. These techniques ensure that networks are efficient, reliable, and capable of handling increasing amounts of data.
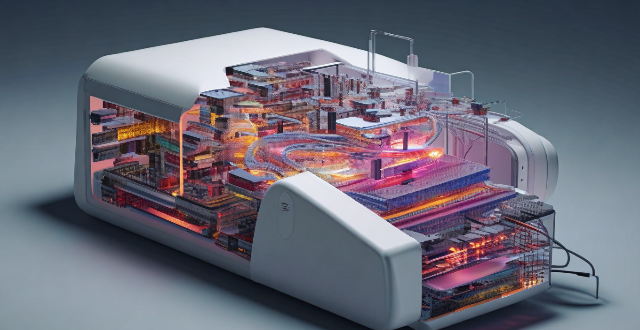
What technology is used in network expansion ?
The text describes various technologies and techniques used in network expansion to increase capacity and coverage, including fiber optics, wireless technologies, software-defined networking (SDN), network function virtualization (NFV), cloud computing, edge computing, network automation and orchestration, multiprotocol label switching (MPLS), cable modems and DSL technology, and submarine cables. Each technology is described in terms of its benefits and how it contributes to network expansion.

How does a network bridge improve internet connectivity ?
A network bridge is a device that connects two or more networks at the data link layer, offering benefits such as reduced congestion, increased security, enhanced performance, cost-effectiveness, and compatibility. It improves internet connectivity by segregating traffic, filtering based on MAC addresses, optimizing routing, and extending the use of existing infrastructure. Bridges are applicable in home, enterprise, and public access networks for connecting devices, separating departmental networks, and providing guest access.
How do QoS (Quality of Service) settings enhance network performance ?
Quality of Service (QoS) settings enhance network performance by prioritizing traffic, allocating bandwidth, managing congestion, and improving user experience. This is achieved through mechanisms such as traffic prioritization, bandwidth allocation, congestion management techniques, shaping and policing, and improved user experience. By implementing QoS strategies effectively, network administrators can ensure that critical applications receive the necessary resources and achieve optimal network performance.
How do compression algorithms contribute to network optimization ?
Compression algorithms are crucial for network optimization by reducing data transmission, thus improving speed, bandwidth consumption, and network performance. They also enhance security and disaster recovery capabilities.

What is network slicing in telecommunications ?
Network slicing allows for multiple virtual networks on a shared physical infrastructure, enabling service providers to offer customized services with specific QoS requirements. Key features include customization, resource allocation, isolation, and flexibility. Benefits include improved efficiency, enhanced security, faster deployment, and better customer experience. Use cases range from smart cities to industrial IoT, telehealth, and enterprise services. Challenges in implementation include complexity, standardization, security concerns, and cost implications. The future outlook is promising, with network slicing expected to play a crucial role in enabling new services and applications as 5G technology becomes more widespread.

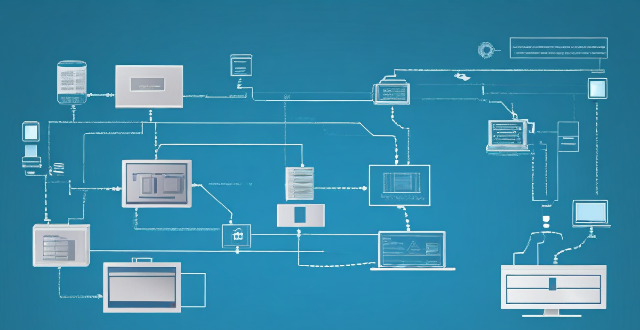
What role does software-defined networking (SDN) play in enabling network slicing ?
Network slicing is a key feature of 5G networks that allows operators to create multiple virtual networks on top of a shared physical infrastructure. SDN plays a crucial role in enabling network slicing by providing the necessary flexibility and programmability to manage and control the network resources. The SDN architecture consists of three main components: the data plane, the control plane, and the management plane. SDN enables network slicing by providing a centralized view of the network resources and allowing operators to dynamically allocate these resources to different slices based on their QoS requirements. Key benefits of SDN for network slicing include flexibility, programmability, centralized control, and resource optimization. Use cases for SDN in network slicing include mobile broadband, IoT, and enterprise networks.

Is network slicing secure for sensitive data transmission ?
Network slicing is a technology that allows multiple virtual networks to coexist on a shared physical infrastructure, enabling service providers to offer customized services with different QoS requirements. While network slicing offers numerous benefits such as customization, resource allocation, scalability, and isolation, there are also potential security concerns that need to be addressed. These include data isolation, access control, encryption, and intrusion detection and prevention systems (IDPS). By implementing robust isolation mechanisms, access control policies, strong encryption algorithms, and effective IDPS, service providers can leverage network slicing while maintaining the security of sensitive data transmission.
What factors affect wireless network coverage ?
**Wireless network coverage is influenced by multiple factors that include physical obstructions, distance from the access point, interference from other devices, environmental conditions, network infrastructure, device capabilities, regulatory limitations, and security settings.**

Can network expansion solve issues related to network congestion ?
## Topic Summary: Network Expansion as a Solution to Network Congestion Network congestion is a common problem that affects the performance of networks, leading to delays and reduced efficiency. One potential solution to this issue is network expansion, which involves increasing the capacity of the existing infrastructure by adding more hardware or upgrading existing equipment. This approach can alleviate network congestion by providing additional bandwidth for data transmission, improving overall performance, and reducing latency. However, network expansion also has its drawbacks, including high costs and the need for careful planning and implementation. Additionally, addressing the underlying causes of congestion is crucial for long-term success.
What are the best tools and technologies for network security protection ?
This article discusses some of the best tools and technologies for network security protection. The list includes firewalls, intrusion detection systems (IDS) and intrusion prevention systems (IPS), virtual private networks (VPNs), antivirus and anti-malware software, next-generation firewalls (NGFWs), network access control (NAC), and security information and event management (SIEM). These tools and technologies can help organizations protect their networks from unauthorized access, data breaches, and other cyber threats. However, it's essential to remember that no single tool or technology can provide complete protection on its own. A layered approach combining multiple solutions is often the most effective way to safeguard your network against today's complex threats.

What are the benefits of using network slicing for businesses ?
Network slicing technology allows businesses to create multiple virtual networks on a shared physical infrastructure, offering benefits such as improved performance, cost efficiency, enhanced security, faster time-to-market, and increased innovation potential.
What is the importance of having a good network coverage ?
The text discusses the importance of having a good network coverage in today's world where communication and connectivity are essential aspects of our daily lives. It outlines several reasons why having a strong and reliable network coverage is crucial, including improved communication, better access to information, enhanced productivity, entertainment on the go, safety and security, and business growth and opportunities. The text concludes that having a good network coverage is an integral part of our modern lifestyle and should not be overlooked when choosing a service provider or planning internet usage.