Data Communication

How does a communication protocol differ from a data format ?
### Topic Summary: Communication Protocol vs. Data Format This topic discusses the differences between communication protocols and data formats, two critical aspects of data exchange in computer systems. A communication protocol is a set of rules that govern how devices or systems communicate with each other, including syntax, semantics, and timing. On the other hand, a data format defines the structure or layout of data for storage or transmission, focusing on the organization of bits, bytes, or fields and their encoding. The main differences between these two concepts are their purpose, scope, and complexity. Communication protocols deal with the entire process of data exchange, including error handling, flow control, and congestion control, while data formats focus solely on the structure of the data. Examples provided include HTTP as a communication protocol and JSON as a data format, which can be used within various communication protocols to send structured data. In summary, communication protocols are like the rules of a conversation, defining how devices interact, while data formats are like the language used in those conversations, specifying how the information is structured and encoded.
How does encryption work in securing communication channels ?
Encryption is a fundamental technique used to secure communication channels by transforming plaintext data into an unreadable format, known as ciphertext. It involves two main processes: encryption and decryption, and uses algorithms and keys for these processes. There are two primary types of encryption methods: symmetric and asymmetric. Encryption ensures that even if data is intercepted during transmission, it remains unreadable to unauthorized parties. It is vital in various applications to secure communication channels, including email, web browsing, mobile communications, and file transfers.

What is the significance of communication protocols in cloud computing ?
In the realm of cloud computing, communication protocolsIn the realm of cloud computing, communication protocols role in facilitating communication protocols play a pivotal role in facilitating seamless and efficient data exchange between various components of a cloud infrastructure. These protocols ensure that data is transmitted reliably and securely across different platforms, devices, and applications within the cloud ecosystem. This article delves into the significance of communication protocols in cloud computing by highlighting their key functions and benefits.
What are the key features of the latest smartphones in terms of communication technology ?
The latest smartphones feature advanced communication technologies including 5G connectivity for high-speed data transfer and improved latency, dual SIM support for simultaneous use of two networks with smart switching, Wi-Fi 6 for faster speeds and better battery life, and Bluetooth 5.x for longer range and faster data transfer. These advancements enhance user experience and pave the way for future innovations in mobile communication technology.

How do communication protocols ensure data integrity and security during transmission ?
The text discusses the role of communication protocols in ensuring data integrity and security during transmission. It outlines mechanisms such as checksums, sequence numbers, acknowledgments for maintaining data integrity, and encryption, authentication, and secure protocols for ensuring data security. The article emphasizes that adhering to these rules allows devices to communicate reliably and securely over networks.

How do communication satellites enable real-time data transmission and monitoring ?
Communication satellites play a crucial role in enabling real-time data transmission and monitoring by serving as relay stations in space that can receive signals from one location on Earth and transmit them to another location. This is achieved through a complex system of technology, infrastructure, and protocols. Satellites are positioned in orbits around the Earth, either in geostationary orbit (GEO) or lower Earth orbit (LEO). Geostationary satellites remain fixed over a specific point on the Earth's surface, while LEO satellites move relative to the Earth's surface. The process begins when a signal, such as a phone call, internet data, or video feed, is generated at a source location. The signal is then sent via a ground station, which has powerful transmitters and antennas, up to the communication satellite using radio waves. Once the satellite receives the signal, it amplifies and frequencies it to avoid interference with other signals. The amplified signal is then transmitted back down to Earth, where another ground station receives it. Finally, the received signal is distributed to its intended destination, such as a phone network, the internet, or a monitoring station. Real-time monitoring is facilitated by the speed at which data can travel via satellite. With modern technology, latency (the time delay in signal transmission) can be minimized, especially with LEO satellites due to their closer proximity to Earth. Satellites can also be networked to provide redundancy and increased bandwidth for large-scale monitoring systems. Key technologies and infrastructure include ground stations, satellite design, network protocols, and satellite constellations. However, there are challenges and considerations such as weather impact, geographical constraints, and regulatory issues. In summary, communication satellites enable real-time data transmission and monitoring by acting as high-altitude relay stations, utilizing advanced technologies and infrastructure to deliver signals across vast distances with minimal delay.
How do communication satellites support military operations and intelligence gathering ?
This text discusses how communication satellites support military operations and intelligence gathering, highlighting their role in secure communication channels, wide area coverage, high-speed data transmission, surveillance and reconnaissance, coordination and command, resilience and redundancy.
What are the benefits and drawbacks of using visual aids in climate science communication ?
Visual aids in climate science communication can enhance comprehension, engagement, and universal appeal but may oversimplify data or mislead if not accurately designed. Creators must balance benefits and drawbacks for effective communication.

How does satellite communication compare to other forms of communication ?
Satellite communication offers global coverage, high capacitySatellite communication offers global coverage, high capacity higher latency and initial costs and reliability but has higher latency and initial costs compared to terrestrial and wireless communication. Terrestrial communication provides lower latency and moderate reliability at a lower cost, while wireless communication offers convenience and portability at a variable cost. Satellite communication is suitable for remote areas and sensitive applications due to its security features.
What is the role of cybersecurity in protecting communication systems ?
The text discusses the importance of cybersecurity in protecting communication systems by ensuring data confidentiality, integrity, and availability. It outlines measures such as encryption techniques, access control, digital signatures, hash functions, network uptime, redundancy, and disaster recovery plans. Additionally, it suggests best practices like regular updates, firewalls, user awareness training, strong authentication mechanisms, and incident response plans to enhance cybersecurity in communication systems.

How does altitude affect communication interference ?
This article discusses how altitude affects communication interference in wireless communication. It explains the various ways that altitude can impact signal strength, including signal attenuation, refraction and scattering, ionospheric effects, and multipath propagation. The article also provides tips for mitigating these effects, such as increasing transmitter power, using higher frequencies, implementing error correction techniques, using directional antennas, and choosing suitable locations for equipment. Overall, understanding altitude's impact on communication interference is crucial for ensuring effective communication in wireless systems.

Can solar flares cause communication interference ?
Solar flares, intense bursts of radiation from the sun's atmosphere, can disrupt communication systems on Earth. This includes shortwave radio signals, satellite communications, and other terrestrial networks. The effects range from signal quality disruption and frequency deviation to satellite link disruptions, GPS accuracy issues, and even physical damage to satellite hardware. While these impacts vary, organizations involved in critical communication operations must be aware of the risks and implement mitigation strategies to minimize potential disruptions.
How do wireless communication standards impact internet speeds ?
This article discusses the impact of wireless communication standards on internet speeds, highlighting key factors such as frequency bands, modulation techniques, multiplexing techniques, error correction codes, and MIMO technology. It explains how these factors contribute to faster data transfer rates, increased network capacity, reliable connections, and improved internet speeds. The article emphasizes the importance of choosing the right wireless communication standard for optimal internet speeds.

How have communication protocols evolved over time ?
The evolution of communication protocols has significantly impacted modern communication systems, transitioning from simple analog signals to complex digital networks. Early communication systems were limited in speed and reliability, but laid the foundation for future advancements. The digital revolution introduced packet switching, leading to protocols like X.25 and Frame Relay. The Internet Protocol Suite (TCP/IP) standardized communication over the internet, enabling global connectivity and applications like email and web browsing. Wireless protocols like Wi-Fi and Bluetooth allowed mobile devices to communicate without physical connections. Future developments may include 5G networks, quantum communication, and IoT protocols. Overall, the evolution of communication protocols has greatly enhanced our ability to connect and access information.
What role does satellite communication play in space exploration and research ?
Satellite communication is crucial for space exploration and research, enabling data collection, real-time communication, navigation, and international collaboration. It will continue to play a vital role in future applications such as deep space exploration, autonomous robotics, and quantum communication.

What are the potential risks associated with mobile communication technology ?
The text discusses the potential risks associated with mobile communication technology, which include security risks such as data breaches and malware attacks, privacy risks like location tracking and surveillance, health risks including radiation exposure and eye strain, social risks such as addiction and cyberbullying, and economic risks involving high costs of data plans and job displacement. It emphasizes the importance of being aware of these risks and taking appropriate measures to mitigate them.

What are some examples of wireless communication protocols ?
This article provides an introduction to wireless communication protocols, which are sets of rules and standards that enable devices to communicate with each other without the use of physical cables. It discusses several examples of wireless communication protocols, including Bluetooth, Wi-Fi, Zigbee, and LoRaWAN. Each protocol has its own unique features and benefits, making them suitable for different applications. For example, Bluetooth is commonly used for connecting devices such as smartphones, headphones, keyboards, and mice, while Wi-Fi is used for connecting devices to the internet or other networks. Zigbee is commonly used in home automation systems, and LoRaWAN is commonly used in IoT applications. By understanding these protocols, developers can create innovative solutions that improve our daily lives.

What role do communication protocols play in IoT (Internet of Things) devices ?
Communication protocols in IoT devices are crucial for data transmission, interoperability, scalability, security, and error handling. Common protocols include MQTT, CoAP, Zigbee, Bluetooth Low Energy, and LoRaWAN, each with specific features like lightweight design, mesh networking, energy efficiency, long-range communication, and broadcast capabilities. These protocols enable seamless interaction between devices and will continue to drive innovation in the IoT field.

How do firewalls contribute to communication security ?
Firewalls play a crucial role in ensuring communication security by acting as a barrier between trusted and untrusted networks. They contribute to communication security through packet filtering, stateful inspection, application-level gateways, content filtering, network address translation (NAT), VPN support, and integration with Intrusion Prevention Systems (IPS). These features help in preventing unauthorized access, protecting against malicious traffic, scanning for viruses, filtering specific types of data, hiding internal network structures, ensuring secure remote access, and detecting potential attacks or policy violations in real-time. Overall, firewalls provide multiple layers of protection, effectively managing and controlling network traffic to secure communications and protect against various types of cyber threats.

How do communication satellites improve global connectivity ?
Communication satellites play a crucial role in enhancing global connectivity by providing reliable and high-speed internet access to remote areas, facilitating international communication, and supporting various applications such as telemedicine, e-learning, and disaster management. They cover vast geographic areas, including mountainous regions, deserts, and oceans, where traditional infrastructure is not feasible or cost-effective. Satellite internet services can be deployed quickly, often within days or weeks, compared to months or years required for terrestrial networks. They enable seamless communication across national borders, fostering global cooperation and collaboration. Newer generations of low Earth orbit (LEO) satellites reduce latency by orbiting closer to Earth, improving the speed and quality of international communication. Satellites facilitate telemedicine by providing real-time video conferencing between patients and healthcare professionals located far apart. They enable e-learning by connecting students in remote areas with educational resources and teachers around the world. During natural disasters or crises, satellites provide critical communication channels for emergency response teams and affected communities.
How do communication satellites impact the field of telecommunications ?
Communication satellites have revolutionized telecommunications by providing global connectivity, increasing bandwidth, and improving reliability. They allow for communication across vast distances, connecting remote areas with the rest of the world and providing access to telecom services in regions lacking terrestrial infrastructure. Modern satellite systems offer high data rates for faster internet speeds and better voice/video transmissions, supporting multiple services like voice, data, and video conferencing. Satellites also enhance reliability and redundancy as critical backups during disasters and emergencies, creating diverse communication pathways. With rapid deployment capabilities, satellites are ideal for temporary situations like military operations or emergency responses and enable mobile applications. Economically, advancing technology reduces costs, opens new markets, and fosters job creation. Technological advancements include improved modulation techniques and antenna designs for better performance. Environmental considerations involve space debris mitigation and energy efficiency. Overall, satellites significantly impact telecommunications by extending reach, increasing capacity, ensuring reliability, offering flexibility, driving economic growth, and fostering technological advancements while considering environmental implications.

What are the common causes of communication interference ?
Communication interference can occur due to physical barriers like noise and technology issues, language differences, cultural norms, emotional factors, personal biases, misunderstandings, lack of active listening, and poor message construction. Being aware of these causes can help individuals improve their communication skills and minimize disruptions in various contexts.

How can satellite communication be used for emergency response and disaster relief ?
Satellite communication is critical in emergency response and disaster relief, offering global coverage, high availability, scalability, and multipurpose use. It enables immediate alerts, coordination, resource deployment, and medical assistance during emergencies. In disaster relief, it aids damage assessment, information dissemination, infrastructure recovery, and aid distribution. Key technical aspects include satellite phones, VSAT terminals, and data collection through sensors. Proper logistics such as training, maintenance, and partnerships with service providers are crucial for effective utilization. Satellite communication significantly enhances the capability to respond to natural disasters and emergencies, reducing their impact on lives and properties.

What is the impact of communication interference on emergency services ?
Communication interference can significantly impact emergency services by delaying response time, impairing coordination, increasing risk to responders and victims, disrupting technology, and negatively affecting public perception. It is crucial for emergency services to prioritize reliable communication systems and protocols to minimize the impact of interference and ensure effective responses to emergencies.
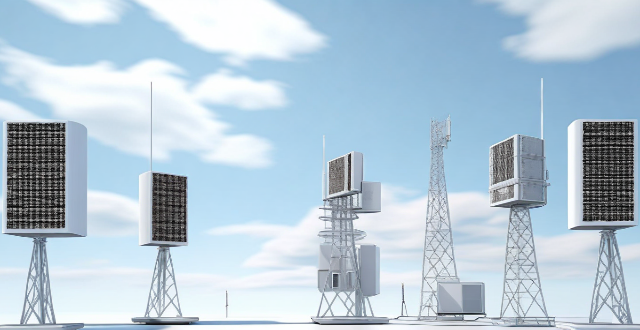
How do communication base stations work ?
Communication base stations, or cell towers, are vital for wireless networks. They consist of antennas, transceivers, controllers, and power supplies to transmit and receive signals. The process includes encoding user data, modulating it onto RF waves, transmitting via antenna arrays, receiving by mobile devices, and decoding back to the original format. Coverage areas depend on antenna height, power, and topography, while handover processes ensure seamless transitions between base stations. Connected to a core network via backhaul links, base stations enable voice calls, messages, and data services, adapting to technological advancements to meet increasing demands.

What are the challenges faced in satellite communication ?
Satellite communication faces challenges such as atmospheric effects, physical obstructions, technical limitations, economic factors, regulatory issues, environmental impacts, security concerns, geopolitical factors, technological advancements, and natural disasters. These challenges highlight the need for innovation and improvement in maintaining reliable satellite communication networks.
How does data encryption affect computer performance ?
Data encryption is crucial for securing data but can affect computer performance by increasing processor load, memory usage, disk I/O, network latency, and reducing battery life.

What are the latest advancements in satellite communication technology ?
Satellite communication technology has seen significant advancements in recent years, including high-throughput satellites (HTS) offering increased bandwidth and improved coverage, low Earth orbit (LEO) satellite constellations providing global coverage with low latency, 5G integrated satellite systems enhancing connectivity and capacity, and quantum satellite networks enabling secure long-distance transmission. These developments are revolutionizing global communication by offering faster speeds, broader access, and enhanced security.

What are the benefits of using mobile communication technology in businesses ?
The text discusses the advantages of utilizing mobile communication technology in business operations. The key benefits include increased mobility and flexibility for employees, improved communication and collaboration among team members, enhanced customer engagement through various platforms, greater efficiency and productivity due to automation and streamlining processes, cost savings by reducing reliance on traditional office spaces, better data collection and analysis for informed decision-making, and improved access to information for employees. These advantages contribute to making businesses more competitive and adaptable to the evolving needs of customers and employees.

How does social engineering pose a risk to communication security ?
The Risks of Social Engineering to Communication Security discusses the dangers of social engineering, a form of manipulation that tricks people into sharing confidential information. Social engineering is a significant threat to communication security because it can infiltrate trusted environments, manipulate human emotions, be difficult to detect, use a variety of attack vectors, lead to data breaches, and lack awareness and training. To protect against social engineering attacks, organizations must implement comprehensive security awareness programs, establish strict verification procedures for sensitive requests, and create a culture of security where employees are encouraged to report suspicious activities without fear of reprimand.